Introduction
A decade ago, enterprise security strategies revolved around protecting a clearly defined perimeter. Applications lived inside corporate data centers, employees worked from managed devices, and traffic flowed through predictable network boundaries. Firewalls, VPN concentrators, and appliance-based intrusion detection systems handled most security requirements.
That world barely exists anymore.
Today’s infrastructure is distributed across public clouds, private clouds, SaaS platforms, edge environments, and containerized workloads. Applications scale dynamically. Microservices communicate across ephemeral environments. Developers deploy updates multiple times per day using CI/CD pipelines. Remote teams connect from everywhere.
Traditional security models weren’t designed for this level of complexity.
That’s why cloud native security has moved from a niche architectural concept to a foundational requirement for modern infrastructure protection. Organizations are realizing that legacy security systems create operational bottlenecks, visibility gaps, and serious risk exposure in cloud environments.
Cloud-native security doesn’t just add security controls to the cloud. It fundamentally changes how security is embedded into infrastructure, workloads, applications, identity management, and deployment pipelines.
And that shift is reshaping enterprise cybersecurity strategy across every major industry.
The Shift From Traditional Infrastructure to Cloud-Native Architecture
Modern infrastructure operates very differently from legacy IT environments.
Traditional systems relied heavily on:
- Static servers
- Monolithic applications
- On-premise hardware
- Fixed network boundaries
- Manual provisioning
- Centralized security enforcement
Cloud-native environments introduce entirely different operational characteristics:
- Containers
- Kubernetes orchestration
- Infrastructure as Code (IaC)
- Elastic compute scaling
- API-driven services
- Distributed workloads
- Continuous deployment pipelines
- Multi-cloud architectures
This architectural evolution dramatically increases agility, but it also expands the attack surface.
A single Kubernetes cluster may spin up thousands of ephemeral containers daily. APIs communicate constantly between microservices. Developers push code multiple times per hour. Cloud workloads appear and disappear dynamically.
Legacy security tools struggle to keep up because they depend on static assumptions about infrastructure.
Cloud-native security models are built specifically for dynamic environments where automation, scalability, and real-time visibility matter more than perimeter enforcement.
What Is Cloud-Native Security?
Cloud-native security refers to security practices, technologies, and operational models specifically designed for cloud-based, containerized, and highly dynamic infrastructure environments.
Instead of treating security as a separate perimeter layer, cloud-native security integrates protection directly into:
- Applications
- Containers
- APIs
- Workloads
- CI/CD pipelines
- Kubernetes orchestration
- Identity systems
- Infrastructure provisioning
The core philosophy is simple:
Security must move at the same speed as modern infrastructure.
That means security controls need to be:
- Automated
- Scalable
- API-driven
- Policy-based
- Continuously monitored
- Integrated into DevOps workflows
Cloud-native security also emphasizes “shift-left” security practices, where vulnerabilities are identified earlier in the software development lifecycle instead of after deployment.
Why Legacy Security Systems Are Failing Modern Infrastructure
Static Perimeter Security No Longer Works
Legacy systems assumed there was a secure internal network and an untrusted external internet.
Cloud computing destroyed that boundary.
Employees access resources from remote locations. Applications run across multiple cloud providers. APIs expose services publicly. Third-party integrations constantly exchange data.
The perimeter has effectively disappeared.
Traditional firewalls still play a role, but they can’t provide complete visibility into container traffic, microservices communication, or cloud-native workloads.
Legacy Tools Lack Cloud Visibility
Most traditional security platforms were built for physical servers and static virtual machines.
They often struggle to monitor:
- Kubernetes clusters
- Serverless workloads
- Container runtime activity
- Ephemeral infrastructure
- API-to-API communication
- Infrastructure-as-Code deployments
This creates blind spots that attackers can exploit.
Cloud-native security tools are designed to observe infrastructure continuously, even as environments scale dynamically.
Manual Security Processes Cannot Scale
Modern DevOps environments deploy software rapidly.
Some organizations push production updates hundreds of times daily.
Manual approval processes, ticket-based security reviews, and legacy compliance workflows create friction that slows development teams.
As a result, security becomes bypassed rather than integrated.
Cloud-native security automates policy enforcement, vulnerability scanning, compliance validation, and runtime monitoring directly inside development pipelines.
Traditional Security Architecture Creates Operational Bottlenecks
Legacy security models often centralize control through dedicated security teams.
That approach breaks down in cloud-native environments because infrastructure changes too quickly.
Developers, DevOps engineers, platform teams, and SREs now share responsibility for security posture.
Cloud-native security enables distributed ownership while maintaining centralized governance through automation and policy-as-code frameworks.
Core Components of Cloud-Native Security
Container Security
Containers transformed software deployment because they package applications with dependencies into portable, lightweight runtime environments.
But container adoption introduced new risks.
Attackers increasingly target:
- Vulnerable container images
- Misconfigured registries
- Insecure runtime permissions
- Privileged containers
- Exposed secrets
- Software supply chain weaknesses
Container security focuses on protecting workloads throughout the entire container lifecycle.
Key Container Security Practices
Image Scanning
Security platforms scan container images for:
- Known CVEs
- Malware
- Outdated dependencies
- Embedded secrets
- Misconfigurations
This typically happens during CI/CD builds before deployment.
Runtime Protection
Runtime security monitors live container behavior for suspicious activity such as:
- Privilege escalation
- Unauthorized process execution
- Network anomalies
- Crypto mining
- Lateral movement attempts
Least Privilege Enforcement
Containers should operate with minimal permissions.
Excessive privileges dramatically increase risk exposure if a container becomes compromised.
Kubernetes Security
Kubernetes has become the standard orchestration platform for cloud-native applications.
But Kubernetes environments are notoriously complex.
Misconfigurations remain one of the largest causes of cloud breaches.
Common Kubernetes Security Risks
Overly Permissive RBAC Policies
Role-Based Access Control (RBAC) determines what users and workloads can access inside Kubernetes clusters.
Poorly configured permissions allow attackers to escalate privileges quickly.
Exposed Kubernetes Dashboards
Unsecured dashboards remain a frequent attack vector in improperly configured clusters.
Insecure Secrets Management
Hardcoded credentials and exposed secrets inside configuration files create serious vulnerabilities.
Cluster Misconfiguration
Open ports, weak network segmentation, and insecure API server settings can expose clusters publicly.
Kubernetes Security Best Practices
Network Segmentation
Microsegmentation restricts communication between workloads.
This limits lateral movement if attackers compromise a container.
Admission Controllers
Admission controllers enforce security policies before workloads deploy into clusters.
Policy-as-Code
Tools like Open Policy Agent (OPA) allow organizations to define and automate governance rules.
Continuous Monitoring
Kubernetes environments require continuous visibility into workloads, APIs, and cluster behavior.
Cloud Workload Protection
Cloud workload protection platforms (CWPPs) secure workloads across:
- Virtual machines
- Containers
- Kubernetes clusters
- Serverless functions
- Hybrid cloud environments
CWPP solutions typically provide:
- Vulnerability management
- Runtime protection
- Behavioral analytics
- Threat detection
- Compliance monitoring
- Configuration assessment
Modern enterprises increasingly use CWPPs because workloads now span multiple infrastructure environments simultaneously.
Identity and Access Management in Cloud Environments
Identity has become the new perimeter.
Cloud-native security prioritizes authentication, authorization, and identity governance rather than relying solely on network-based defenses.
Critical IAM Principles
Least Privilege Access
Users and services should only receive permissions required for specific tasks.
Short-Lived Credentials
Temporary credentials reduce exposure if secrets become compromised.
Multi-Factor Authentication
MFA remains one of the most effective defenses against credential theft.
Federated Identity
Centralized identity providers simplify authentication across distributed systems.
Zero Trust Cloud Security
Zero trust cloud security assumes that no user, device, workload, or service should automatically be trusted.
Every request requires verification.
This model is particularly important in cloud-native environments where infrastructure boundaries constantly shift.
Core Zero Trust Principles
Verify Explicitly
Authentication and authorization occur continuously.
Assume Breach
Security models must anticipate compromise and minimize blast radius.
Enforce Least Privilege
Access is restricted to necessary resources only.
Segment Aggressively
Microsegmentation reduces lateral movement opportunities.
How DevOps and Cloud-Native Security Work Together
Cloud-native security and DevOps are deeply interconnected.
Traditional security approaches often created friction between development and security teams.
Cloud-native models aim to eliminate that conflict.
This gave rise to DevSecOps.
DevSecOps integrates security directly into:
- CI/CD pipelines
- Source control systems
- Infrastructure provisioning
- Automated testing
- Deployment workflows
Shift-Left Security
Shift-left security moves vulnerability detection earlier in the development lifecycle.
Instead of discovering issues after deployment, teams identify risks during:
- Code commits
- Build stages
- Dependency analysis
- Infrastructure provisioning
- Container creation
This reduces remediation costs significantly.
Infrastructure as Code Security
Infrastructure as Code tools like Terraform and CloudFormation automate environment provisioning.
However, insecure IaC templates can propagate vulnerabilities rapidly.
Cloud-native security platforms scan IaC templates for:
- Publicly exposed storage
- Weak encryption settings
- Excessive permissions
- Insecure networking rules
- Compliance violations
Real-World Security Challenges in Multi-Cloud Environments
Most enterprises no longer operate within a single cloud provider.
Organizations commonly combine:
- Amazon Web Services
- Microsoft Azure
- Google Cloud Platform
- Private cloud infrastructure
- SaaS ecosystems
This creates enormous operational complexity.
Common Multi-Cloud Security Challenges
Inconsistent Security Policies
Different cloud providers use different security models, APIs, and configurations.
Fragmented Visibility
Security teams struggle to monitor infrastructure consistently across providers.
Compliance Management
Regulatory requirements become harder to enforce across distributed systems.
Identity Sprawl
Multiple cloud accounts increase credential management complexity.
Cloud-native security platforms help unify policy enforcement and visibility across heterogeneous environments.
Benefits of Cloud-Native Security Models
Faster Threat Detection
Cloud-native monitoring provides real-time telemetry and behavioral analytics.
Threats can often be detected within minutes rather than days.
Improved Scalability
Security controls scale automatically alongside infrastructure growth.
This is critical for elastic cloud workloads.
Better Developer Productivity
Integrated security tooling reduces deployment friction.
Developers receive faster feedback during builds and deployments.
Reduced Attack Surface
Microsegmentation, least privilege enforcement, and workload isolation reduce exposure.
Enhanced Compliance Automation
Automated compliance checks simplify adherence to frameworks such as:
- SOC 2
- ISO 27001
- HIPAA
- PCI DSS
- GDPR
Common Mistakes Organizations Make During Migration
Treating Cloud Security Like Traditional Security
Simply lifting legacy controls into cloud infrastructure rarely works effectively.
Cloud-native environments require fundamentally different operating models.
Ignoring Shared Responsibility Models
Cloud providers secure the underlying infrastructure, but customers remain responsible for:
- Identity management
- Workload security
- Application security
- Data protection
- Configuration management
Misunderstanding this responsibility split leads to major security gaps.
Overlooking Runtime Security
Many organizations focus heavily on prevention while neglecting runtime detection and response.
Attackers increasingly exploit runtime weaknesses after deployment.
Failing to Secure APIs
APIs are central to cloud-native architectures.
Weak API authentication, excessive exposure, and poor rate limiting create serious vulnerabilities.
Cloud-Native Security Tools and Platforms
The cloud-native security ecosystem has evolved rapidly.
Categories of Modern Security Platforms
CNAPP Platforms
Cloud-Native Application Protection Platforms combine:
- CSPM
- CWPP
- CIEM
- Container security
- Kubernetes security
into unified solutions.
CSPM Solutions
Cloud Security Posture Management platforms identify cloud misconfigurations and compliance issues.
SIEM and Observability Platforms
Modern observability tools integrate logs, metrics, traces, and threat analytics.
Service Mesh Security
Service meshes like Istio improve encryption, traffic control, and workload identity management.
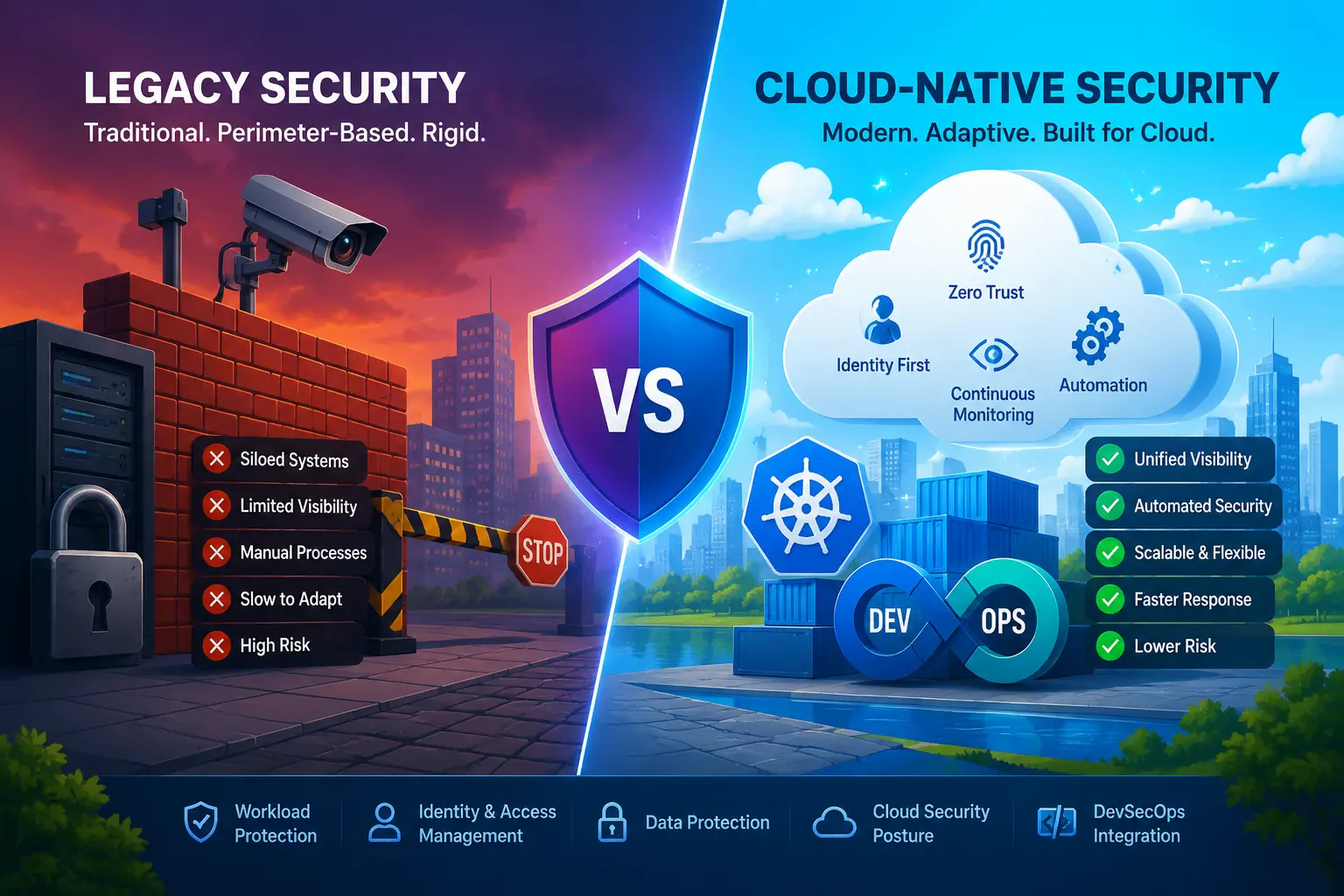
Cloud-Native Security vs Traditional Security
| Area | Legacy Security | Cloud-Native Security |
|---|---|---|
| Architecture | Perimeter-based | Identity and workload-based |
| Infrastructure | Static | Dynamic |
| Deployment | Manual | Automated |
| Scalability | Limited | Elastic |
| Visibility | Partial | Continuous |
| Security Enforcement | Appliance-centric | Policy-driven |
| Threat Detection | Reactive | Real-time |
| Workload Support | Physical/VM-focused | Containers/Kubernetes/serverless |
| DevOps Integration | Minimal | Native |
| Identity Controls | Secondary | Central |
Future Trends in Cloud Infrastructure Protection
Cloud-native security continues evolving rapidly.
Several trends are reshaping the industry.
AI-Driven Threat Detection
Machine learning increasingly helps identify behavioral anomalies across massive telemetry datasets.
Software Supply Chain Security
Organizations now focus heavily on securing:
- Open-source dependencies
- Build pipelines
- Artifact registries
- Code signing
- SBOM management
Confidential Computing
Confidential computing technologies protect workloads during runtime using hardware-based isolation.
Identity-Centric Security
Identity governance will continue replacing network-centric trust models.
Autonomous Security Operations
Automation will increasingly handle:
- Incident response
- Threat correlation
- Policy enforcement
- Compliance remediation
FAQ
What is cloud-native security?
Cloud-native security refers to security practices and technologies designed specifically for cloud-based, containerized, and highly dynamic infrastructure environments. It integrates security directly into workloads, applications, Kubernetes clusters, APIs, and CI/CD pipelines.
Why are legacy security systems becoming obsolete?
Legacy systems rely heavily on static network perimeters and manual processes. Modern cloud environments are dynamic, distributed, and API-driven, making traditional security models insufficient for visibility, scalability, and threat detection.
What is Kubernetes security?
Kubernetes security involves protecting container orchestration environments through controls such as RBAC management, network policies, secrets protection, admission controllers, runtime monitoring, and workload isolation.
What is zero trust cloud security?
Zero trust cloud security assumes no entity should be trusted automatically. Every request must be authenticated, authorized, and continuously validated regardless of location or network origin.
How does cloud workload protection work?
Cloud workload protection platforms monitor workloads across VMs, containers, Kubernetes clusters, and serverless environments. They provide vulnerability scanning, runtime monitoring, behavioral analytics, and compliance enforcement.
Is cloud-native security only for large enterprises?
No. Startups, SaaS companies, SMBs, and mid-market organizations also benefit significantly from cloud-native security practices because modern applications increasingly rely on cloud infrastructure regardless of company size.
What are the biggest cloud-native security risks?
Major risks include:
Misconfigured cloud services
Kubernetes vulnerabilities
Weak identity controls
API exposure
Container supply chain attacks
Excessive permissions
Insecure Infrastructure as Code templates
Conclusion
Cloud-native infrastructure fundamentally changed how applications are built, deployed, and scaled. Security models built for static data centers simply cannot provide the visibility, automation, and agility required in modern cloud environments.
That’s why organizations are shifting toward cloud-native security architectures centered around identity, automation, workload protection, Kubernetes governance, and zero trust principles.
The transition isn’t just about better tooling.
It’s about aligning security with the operational reality of modern software delivery.
Enterprises that successfully adopt cloud-native security gain more than stronger protection. They improve deployment velocity, operational resilience, compliance automation, and infrastructure scalability simultaneously.
As cloud adoption accelerates, cloud-native security is quickly becoming the default foundation for modern infrastructure protection.