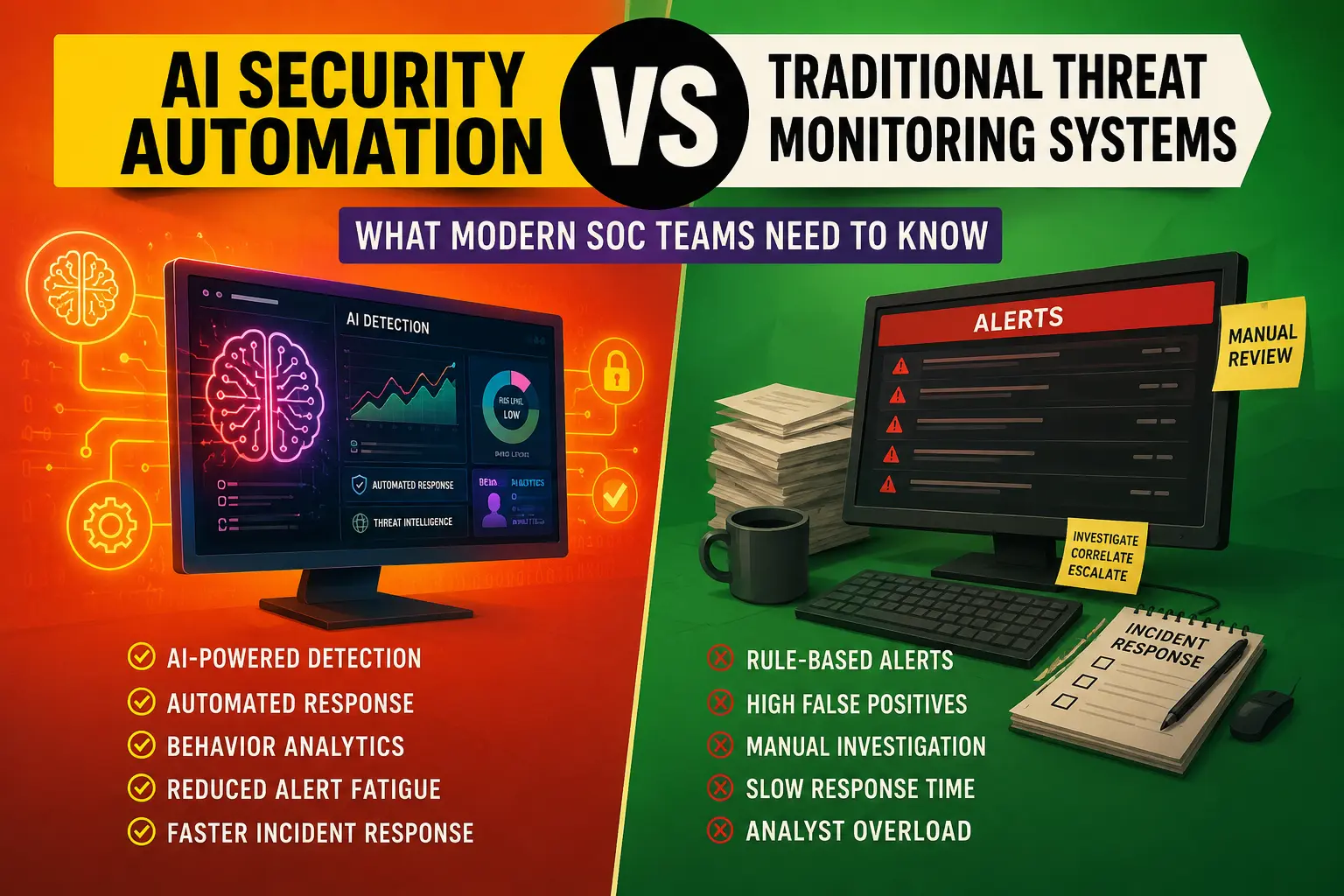
AI Security Automation vs Traditional Threat Monitoring Systems
Enterprise security operations have changed dramatically over the last decade. Attack surfaces are larger, cloud infrastructure is more distributed, remote work has become standard, and cyberattacks now move at machine speed. Traditional threat monitoring systems, once considered sufficient for enterprise defense, are struggling to keep up with modern attack complexity.
Security Operations Centers (SOCs) are under constant pressure to investigate thousands of alerts, correlate fragmented telemetry, reduce dwell time, and respond to incidents before attackers escalate privileges or move laterally across the environment. In many organizations, analysts spend more time triaging false positives than investigating real threats.
That operational strain is one of the biggest reasons AI security automation has moved from experimental technology to a core cybersecurity investment area.
Modern AI SOC tools combine machine learning, behavioral analytics, automation pipelines, threat intelligence correlation, and orchestration capabilities to improve detection quality and accelerate incident response. Instead of relying entirely on static rules and manual analysis, AI-driven systems continuously learn from data patterns across endpoints, networks, identities, cloud workloads, SaaS platforms, and user behavior.
The result is a major shift in how enterprise threat monitoring works.
But AI security automation is not simply a replacement for traditional monitoring systems. The reality is more nuanced. Most mature enterprises operate hybrid security models where AI enhances analyst workflows rather than replacing them outright.
Understanding the differences between traditional monitoring and AI-powered cybersecurity automation is essential for SOC leaders, security architects, CISOs, and enterprise IT teams evaluating the next generation of security operations platforms.
The Evolution of Enterprise Threat Monitoring
Traditional enterprise threat monitoring evolved around perimeter-centric security models. Organizations protected centralized networks, on-premises infrastructure, and predictable user behavior patterns.
Security teams relied heavily on:
- Signature-based detection
- Rule-based SIEM alerts
- Firewall logs
- IDS and IPS systems
- Antivirus platforms
- Manual threat hunting
- Ticket-driven incident response
This approach worked reasonably well when environments were simpler and attack volumes were manageable.
That landscape no longer exists.
Modern enterprises operate across:
- Multi-cloud environments
- Hybrid infrastructure
- Remote endpoints
- Mobile devices
- SaaS ecosystems
- API-heavy architectures
- Containerized workloads
- Identity-centric access systems
Attackers also evolved. Ransomware groups, advanced persistent threats (APTs), credential theft campaigns, insider threats, and supply chain compromises now use stealthier techniques designed to bypass traditional signatures.
As telemetry volume exploded, SOC teams faced a new problem: visibility without context.
Many organizations collect terabytes of security data daily but still struggle to identify high-priority incidents quickly.
That gap created demand for cybersecurity automation platforms capable of handling scale, correlation, and real-time analysis beyond human capacity.
What Is AI Security Automation?
AI security automation refers to the use of artificial intelligence, machine learning, and automated workflows to detect, investigate, prioritize, and respond to cybersecurity threats with minimal manual intervention.
Modern AI monitoring systems typically integrate with:
- SIEM platforms
- Endpoint Detection and Response (EDR)
- Extended Detection and Response (XDR)
- Identity providers
- Network monitoring tools
- Cloud security platforms
- Threat intelligence feeds
- SOAR platforms
- Vulnerability management systems
Rather than depending solely on predefined detection rules, AI systems analyze patterns, behaviors, anomalies, and correlations across massive datasets.
Core capabilities often include:
Behavioral Analytics
AI systems establish baselines for normal behavior across users, devices, applications, and network traffic. Suspicious deviations trigger investigations automatically.
Automated Threat Detection
Machine learning models identify indicators of compromise, malicious activity patterns, privilege escalation attempts, abnormal authentication behavior, and lateral movement techniques.
Security Orchestration
SOAR-style workflows automate repetitive SOC tasks such as:
- Log enrichment
- IOC correlation
- Ticket creation
- Containment actions
- Endpoint isolation
- User suspension
- Threat intelligence lookups
Threat Prioritization
AI systems score alerts based on risk context, reducing analyst overload and improving investigation efficiency.
Continuous Learning
Unlike static rule engines, AI monitoring systems improve over time as they process more telemetry and analyst feedback.
How Traditional Threat Monitoring Systems Work
Traditional monitoring systems are fundamentally rule-driven.
Security teams configure:
- Correlation rules
- Signature databases
- Threshold alerts
- Static detection logic
- IOC matching systems
These platforms generate alerts when predefined conditions occur.
For example:
- Multiple failed logins
- Malware hash matches
- Suspicious port scanning
- Known malicious IP communication
- Unauthorized privilege escalation
- Firewall policy violations
This model still plays an important role in enterprise cybersecurity because deterministic detection remains highly effective for known threats.
However, traditional monitoring systems face several limitations.
High False Positive Rates
Static rules often lack contextual understanding. Legitimate business activity can trigger large volumes of alerts.
Limited Adaptability
Traditional systems struggle against novel attack techniques that do not match existing signatures or detection logic.
Manual Investigation Burden
Analysts must manually correlate logs, investigate events, enrich alerts, and determine severity.
Slow Incident Response
Escalation workflows often depend heavily on human intervention and ticket routing.
Scalability Constraints
As infrastructure grows, alert volume frequently increases faster than SOC staffing levels.
Core Differences Between AI Security Automation and Traditional Monitoring
Detection Methodology
Traditional systems rely on predefined rules.
AI-driven systems use adaptive analysis, behavioral modeling, anomaly detection, and probabilistic risk scoring.
Operational Speed
AI systems process massive telemetry streams in near real time, reducing investigation delays.
Traditional SOC workflows are often bottlenecked by manual review processes.
Contextual Awareness
AI monitoring platforms correlate data from multiple sources simultaneously.
Traditional systems frequently analyze events in isolation.
Threat Adaptability
Machine learning models can identify previously unseen attack patterns.
Signature-based systems are generally reactive.
Workflow Automation
AI security automation platforms orchestrate investigations and containment automatically.
Traditional systems usually require analyst-driven response actions.
Detection Speed and Response Efficiency
Speed matters enormously in cybersecurity.
Attackers can move laterally across enterprise environments within minutes. Ransomware operators often escalate privileges and encrypt systems rapidly after initial compromise.
Traditional monitoring systems introduce delays because analysts must:
- Review alerts
- Validate events
- Enrich indicators
- Correlate telemetry
- Assess severity
- Escalate incidents
- Trigger response procedures
AI SOC tools compress these workflows significantly.
For example, an AI-driven detection pipeline may automatically:
- Correlate endpoint and identity anomalies
- Compare indicators against threat intelligence
- Map activity to MITRE ATT&CK techniques
- Calculate risk scores
- Trigger automated containment actions
- Generate incident summaries
That reduction in Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) can materially reduce breach impact.
In modern enterprise environments, response speed is often the difference between a contained incident and a large-scale operational disruption.
Alert Fatigue and Analyst Burnout
Alert fatigue remains one of the biggest operational problems in cybersecurity.
Traditional SIEM environments frequently overwhelm SOC analysts with thousands of daily alerts, many of which are low priority or benign.
This creates several downstream problems:
- Missed critical threats
- Analyst burnout
- Slower investigations
- Escalation delays
- High staff turnover
- Reduced operational efficiency
AI security automation addresses this by introducing intelligent alert prioritization.
Instead of presenting every anomaly equally, AI monitoring systems evaluate:
- Behavioral context
- Asset criticality
- User risk profiles
- Threat intelligence confidence
- Historical activity patterns
- Lateral movement indicators
- Privilege escalation attempts
The result is higher-fidelity alerting.
SOC analysts spend less time filtering noise and more time investigating legitimate threats.
This operational improvement is one reason enterprise demand for AI SOC tools continues to rise.
AI SOC Tools and Modern Security Operations Centers
Modern SOC environments increasingly depend on interconnected security ecosystems rather than isolated monitoring tools.
AI SOC platforms commonly integrate:
- EDR
- XDR
- SIEM
- SOAR
- IAM
- CASB
- Cloud workload protection
- Email security gateways
- Network detection systems
This convergence enables broader visibility and faster decision-making.
Key Advantages of AI SOC Platforms
Cross-Domain Correlation
AI systems correlate telemetry across:
- Identity activity
- Endpoint behavior
- Network traffic
- Cloud events
- SaaS logs
- Application telemetry
Autonomous Investigation
Some platforms perform automated evidence gathering before analysts even review the incident.
Threat Intelligence Enrichment
AI systems automatically compare indicators against:
- Known malware infrastructure
- Ransomware campaigns
- Nation-state IOC databases
- Commercial intelligence feeds
Risk-Based Prioritization
High-risk incidents move to the top of analyst queues automatically.
Automated Threat Detection in Enterprise Environments
Automated threat detection is one of the most commercially significant applications of AI in cybersecurity.
Large enterprises generate security telemetry from:
- Active Directory
- Azure AD
- VPN systems
- Cloud workloads
- Kubernetes clusters
- DNS logs
- EDR agents
- Web proxies
- Email platforms
- IAM systems
Manually correlating these datasets is operationally unrealistic at scale.
AI monitoring systems continuously evaluate relationships between events.
For example, an AI-driven engine might identify:
- Impossible travel logins
- Credential stuffing behavior
- Insider threat indicators
- Data exfiltration anomalies
- Command-and-control communication
- Privilege escalation sequences
- Lateral movement patterns
- Living-off-the-land techniques
Traditional rule-based systems often miss these chained behaviors because the signals appear benign individually.
AI models detect the broader attack narrative.
Behavioral Analytics and Machine Learning in Cybersecurity
Behavioral analytics fundamentally changes enterprise threat detection.
Instead of focusing only on known malicious signatures, AI systems learn what “normal” looks like.
Examples include:
- Typical login locations
- Normal file access behavior
- Standard application usage
- Average network transfer volumes
- Expected administrative actions
- Common user workflows
When deviations occur, the system evaluates whether the behavior resembles malicious activity.
This approach is particularly effective against:
- Insider threats
- Credential compromise
- Account takeover
- Zero-day exploitation
- Advanced persistent threats
- Low-and-slow attack patterns
Machine learning models can also identify subtle attack signals hidden within massive datasets.
For example:
A compromised account accessing a sensitive database at 3 AM from an unusual device may not trigger a traditional signature. Behavioral AI systems, however, can detect the contextual anomaly.
Scalability Challenges in Traditional SOC Operations
One of the biggest weaknesses of traditional monitoring systems is operational scalability.
Enterprise telemetry growth is accelerating rapidly due to:
- Cloud migration
- IoT adoption
- Remote work
- API proliferation
- Container orchestration
- SaaS expansion
- Increased compliance logging
Traditional SOC models scale poorly because they depend heavily on human investigation capacity.
Organizations often respond by:
- Hiring more analysts
- Expanding shifts
- Increasing outsourcing
- Adding more SIEM rules
But this creates diminishing returns.
More alerts do not automatically improve security outcomes.
AI security automation changes the scalability equation by allowing organizations to process larger datasets without proportional analyst growth.
That operational efficiency has become a major factor in enterprise cybersecurity budgeting.
Incident Response Automation and Orchestration
Detection is only one part of the SOC workflow.
Response speed matters just as much.
Traditional response processes are frequently fragmented across:
- Email approvals
- Ticketing systems
- Manual playbooks
- Escalation chains
- Spreadsheet tracking
AI-driven cybersecurity automation platforms integrate orchestration directly into incident handling.
Examples of automated response actions include:
- Isolating compromised endpoints
- Disabling suspicious accounts
- Blocking malicious IPs
- Revoking OAuth tokens
- Quarantining phishing emails
- Triggering MFA challenges
- Collecting forensic artifacts
Automation significantly reduces containment time.
It also improves consistency because workflows follow predefined playbooks rather than relying entirely on analyst discretion during high-pressure incidents.
False Positives vs Context-Aware Detection
False positives are expensive.
Every unnecessary investigation consumes analyst time, delays real incident response, and increases operational fatigue.
Traditional rule-based monitoring systems often generate noisy alerts because they lack broader context.
For example:
A privileged login from another region may trigger a critical alert even if the user is legitimately traveling.
AI monitoring systems incorporate contextual intelligence such as:
- User history
- Device trust
- Authentication patterns
- Session behavior
- Asset sensitivity
- Geographic consistency
- Peer-group analysis
This context-aware approach improves detection quality substantially.
However, AI systems are not perfect.
Poorly trained models can still produce false positives or overlook sophisticated attacks if telemetry quality is weak.
Effective AI security automation depends heavily on:
- High-quality data
- Proper tuning
- Continuous validation
- Human oversight
Cloud Security and Hybrid Infrastructure Monitoring
Traditional security monitoring evolved for on-premises infrastructure.
Modern enterprise environments are fundamentally different.
Organizations now operate across:
- AWS
- Microsoft Azure
- Google Cloud
- SaaS ecosystems
- Hybrid data centers
- Edge infrastructure
- Kubernetes environments
This creates visibility fragmentation.
AI monitoring systems help unify security telemetry across distributed environments.
Capabilities often include:
- Cloud workload anomaly detection
- API behavior monitoring
- Container threat detection
- Identity analytics
- SaaS activity analysis
- Multi-cloud correlation
Traditional monitoring systems frequently require extensive manual configuration to achieve comparable visibility.
AI-driven platforms simplify operational management while improving cross-environment threat detection.
Compliance, Governance, and Audit Considerations
Enterprise cybersecurity is not only about threat prevention.
Organizations must also satisfy compliance requirements related to:
- GDPR
- HIPAA
- PCI DSS
- ISO 27001
- SOC 2
- NIST
- CMMC
AI security automation can improve compliance operations by:
- Automating evidence collection
- Maintaining audit trails
- Standardizing incident workflows
- Enforcing policy-based responses
- Monitoring privileged access
- Detecting policy violations
However, governance concerns also exist.
Organizations must address:
- AI transparency
- Model explainability
- Data privacy
- Bias in risk scoring
- Automated decision accountability
Security leaders increasingly require visibility into how AI systems prioritize threats and trigger actions.
Explainable AI is becoming an important requirement in regulated industries.
Cost Analysis and Operational ROI
Enterprise security budgets are under constant scrutiny.
Traditional SOC scaling usually requires additional:
- Analysts
- Tier-1 staffing
- Threat hunters
- SIEM engineers
- Incident responders
Labor costs rise quickly.
AI security automation changes the economics by improving analyst efficiency.
Potential ROI drivers include:
- Lower MTTD
- Reduced MTTR
- Fewer manual investigations
- Reduced false positives
- Smaller alert queues
- Faster containment
- Improved staffing efficiency
That said, AI platforms can also introduce significant costs:
- Licensing fees
- Integration complexity
- Data pipeline expansion
- Training requirements
- Model tuning
- Cloud compute expenses
The best enterprise outcomes usually come from targeted automation rather than attempting to automate every security process simultaneously.
Human Analysts vs AI-Augmented Security Teams
Despite aggressive marketing claims, AI is not replacing SOC analysts entirely.
Experienced security professionals remain essential for:
- Threat hunting
- Strategic analysis
- Incident leadership
- Adversary emulation
- Risk assessment
- Policy decisions
- Complex investigations
AI works best as a force multiplier.
In mature SOC environments, automation handles repetitive and high-volume tasks while analysts focus on higher-level decision-making.
This hybrid model improves both operational efficiency and security quality.
Human expertise still matters enormously when:
- Evaluating ambiguous threats
- Investigating sophisticated attackers
- Understanding business context
- Managing crisis response
- Making legal or compliance decisions
The future SOC is likely AI-augmented rather than fully autonomous.
Common Risks and Misconceptions About AI Security Automation
AI security automation is powerful, but it is not magic.
Several misconceptions create unrealistic expectations.
Misconception: AI Eliminates False Positives
AI reduces noise but does not remove it entirely.
Misconception: Automation Replaces Analysts
Human oversight remains critical.
Misconception: AI Stops Zero-Day Attacks Automatically
AI improves anomaly detection, but sophisticated adversaries can still evade models.
Misconception: More Data Always Improves Detection
Poor-quality telemetry can weaken model performance.
Misconception: AI Security Is Fully Autonomous
Most enterprise AI systems still require:
- Tuning
- Governance
- Oversight
- Workflow management
- Detection engineering
Organizations that treat AI as a complete replacement for security operations often introduce new operational risks.
Real-World Enterprise Use Cases
Financial Services
Banks use AI monitoring systems to detect:
- Fraud
- Account takeover
- Insider abuse
- Unusual transaction behavior
Behavioral analytics is particularly valuable in financial environments where transaction patterns matter.
Healthcare
Healthcare organizations use cybersecurity automation to:
- Protect patient data
- Monitor privileged access
- Detect ransomware activity
- Secure connected medical devices
Manufacturing
Industrial organizations deploy AI monitoring for:
- OT security visibility
- Supply chain threat detection
- Industrial network anomaly analysis
SaaS and Technology Companies
Cloud-native companies use AI SOC tools for:
- Identity-centric security
- API threat detection
- Kubernetes monitoring
- Multi-cloud telemetry correlation
How to Transition from Traditional Monitoring to AI-Driven Security
Enterprises rarely replace legacy monitoring systems overnight.
Most organizations adopt phased modernization strategies.
Step 1: Assess Existing SOC Maturity
Evaluate:
- Current tooling
- Alert quality
- Analyst workflows
- Data visibility gaps
- Incident response bottlenecks
Step 2: Prioritize High-Value Automation Areas
Start with repetitive workflows such as:
- Alert triage
- IOC enrichment
- Phishing analysis
- Endpoint containment
Step 3: Improve Telemetry Quality
AI systems require strong data foundations.
Focus on:
- Log normalization
- Asset inventory accuracy
- Identity visibility
- Endpoint coverage
Step 4: Integrate Threat Intelligence
Context improves AI detection quality significantly.
Step 5: Maintain Human Oversight
Automation should support analysts rather than bypass governance entirely.
Best Practices for Implementing AI Security Automation
Focus on Use Cases First
Avoid adopting AI purely because it is trendy.
Define measurable objectives such as:
- Reducing MTTR
- Lowering alert fatigue
- Improving phishing response
- Increasing detection coverage
Start With Limited Automation
Gradual implementation reduces operational risk.
Continuously Tune Detection Models
Security environments evolve constantly.
Align AI With Existing SOC Processes
Technology alone does not solve operational problems.
Validate Vendor Claims Carefully
Many cybersecurity vendors market basic automation as “AI-powered.”
Evaluate:
- Detection quality
- Explainability
- Integration depth
- Workflow flexibility
- Operational maturity
Future Trends in AI-Powered SOC Operations
Several trends are reshaping enterprise cybersecurity operations.
AI-Native SOC Platforms
New platforms are being designed around automation from the start rather than retrofitting AI onto legacy SIEM architectures.
Autonomous Threat Hunting
AI-assisted hunting models are becoming more proactive.
Generative AI in Security Operations
Large language models are increasingly used for:
- Incident summarization
- Investigation guidance
- Query generation
- Threat analysis support
Identity-Centric Security Analytics
Identity telemetry is becoming a primary detection source.
Predictive Risk Modeling
Future AI systems may identify likely attack paths before exploitation occurs.
FAQ
What is AI security automation?
AI security automation uses artificial intelligence, machine learning, and automated workflows to improve cybersecurity operations such as threat detection, alert prioritization, investigation, and incident response.
How does AI security automation differ from traditional SIEM monitoring?
Traditional SIEM systems rely primarily on static rules and signatures, while AI-driven platforms use behavioral analytics, anomaly detection, and contextual risk analysis to identify threats dynamically.
Can AI replace SOC analysts?
No. AI improves operational efficiency but still requires human oversight, investigation expertise, and strategic decision-making.
What are the benefits of AI SOC tools?
Key benefits include:
Faster threat detection
Reduced alert fatigue
Improved incident response
Better scalability
Automated investigations
Higher operational efficiency
What are the risks of AI cybersecurity automation?
Risks include:
Model bias
Poor telemetry quality
Over-automation
Lack of explainability
False confidence in autonomous systems
Is AI threat detection better for cloud environments?
Yes. AI systems are particularly effective in cloud and hybrid environments because they can correlate telemetry across distributed infrastructure and identity systems.
What industries benefit most from AI security automation?
Industries with large-scale telemetry and strict security requirements benefit significantly, including:
Financial services
Healthcare
Government
Manufacturing
SaaS
Enterprise technology
Does AI reduce false positives?
In many cases, yes. AI monitoring systems improve contextual understanding, which helps prioritize higher-quality alerts and reduce unnecessary investigations.
Conclusion
Traditional threat monitoring systems still play an important role in enterprise cybersecurity, especially for deterministic detection and compliance visibility. But the scale, speed, and complexity of modern attacks have exposed the limitations of purely rule-based security operations.
AI security automation introduces a fundamentally different operational model. By combining behavioral analytics, machine learning, automated workflows, and contextual correlation, modern AI SOC tools help enterprises process massive telemetry volumes more efficiently while improving detection quality and response speed.
The most effective security organizations are not replacing human analysts with AI. They are building AI-augmented SOC operations where automation handles repetitive, high-volume tasks and skilled analysts focus on strategic investigation and response.
As enterprise infrastructure becomes increasingly distributed and attackers continue evolving their tactics, AI-driven cybersecurity automation is quickly becoming a core operational capability rather than an optional enhancement.