DevSecOps vs DevOps: Security Differences Explained
Modern software delivery has changed dramatically over the last decade. Development teams no longer ship updates every few months. Many SaaS platforms now deploy code dozens — sometimes hundreds — of times per day. That speed created enormous pressure on traditional IT operations, which led to the rise of DevOps.
But speed introduced another problem: security gaps.
Organizations accelerated release cycles faster than security practices could evolve. Vulnerabilities started slipping into production environments through CI/CD pipelines, open-source dependencies, insecure APIs, misconfigured containers, and exposed cloud infrastructure.
That’s where DevSecOps entered the picture.
The debate around DevSecOps vs DevOps is no longer theoretical. For software companies, cloud-native startups, fintech platforms, healthcare systems, and enterprise engineering teams, it directly affects release velocity, compliance exposure, customer trust, and breach risk.
The key difference comes down to one principle:
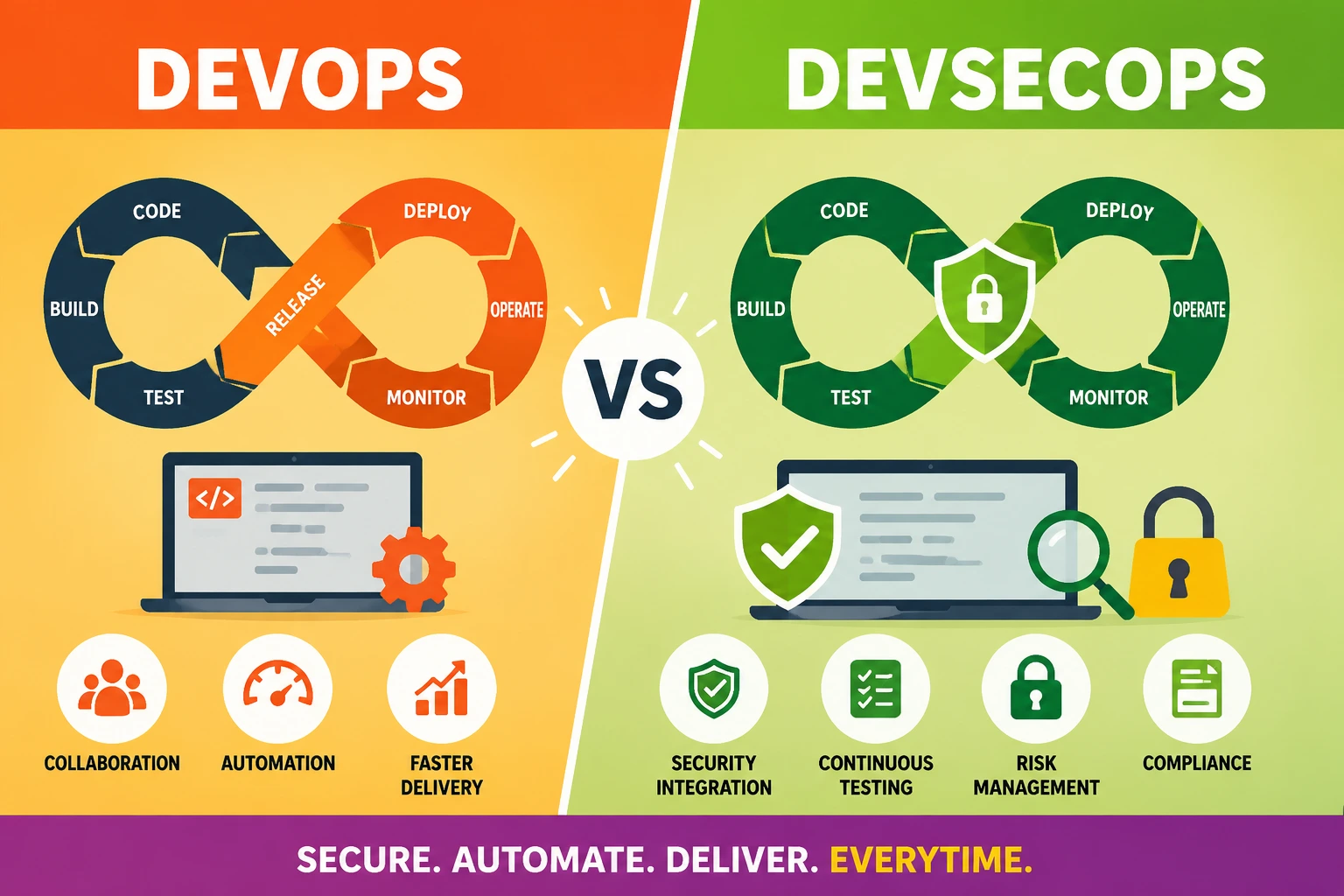
Traditional DevOps treats security as a separate process. DevSecOps embeds security directly into the software delivery lifecycle.
That sounds simple on paper. In practice, it changes everything from pipeline architecture to team responsibilities, tooling, automation, governance, and deployment workflows.
This guide breaks down the real-world security differences between DevSecOps and traditional DevOps, including CI/CD security models, application security testing strategies, infrastructure protection, compliance automation, and operational trade-offs that modern engineering teams face every day.
What Is Traditional DevOps?
Traditional DevOps is a software delivery methodology focused on improving collaboration between development and operations teams.
Before DevOps became mainstream, development teams wrote code while operations teams handled deployments, infrastructure, scaling, monitoring, and production stability. The separation created friction:
- Slow releases
- Deployment failures
- Environment inconsistencies
- Long feedback loops
- Manual operational bottlenecks
DevOps addressed these problems by introducing:
- CI/CD pipelines
- Infrastructure as Code (IaC)
- Automated deployments
- Continuous integration
- Monitoring and observability
- Agile delivery workflows
The goal was simple: deliver software faster and more reliably.
In many traditional DevOps environments, security remained largely outside the pipeline. Security reviews often happened late in the release cycle through:
- Manual penetration testing
- Compliance reviews
- External audits
- Security team approvals
- Periodic vulnerability scans
That approach worked when releases happened quarterly. It breaks down when deployments happen continuously.
What Is DevSecOps?
DevSecOps extends DevOps by integrating security directly into the software development lifecycle.
Instead of treating security as a final checkpoint, DevSecOps embeds automated security validation into every stage of the pipeline.
That includes:
- Secure coding practices
- Dependency scanning
- Static application security testing (SAST)
- Dynamic application security testing (DAST)
- Infrastructure scanning
- Container security
- Runtime monitoring
- Secrets management
- Compliance automation
The core philosophy behind DevSecOps is often summarized as “shift security left.”
That means identifying vulnerabilities earlier in development before they become expensive production incidents.
A DevSecOps pipeline doesn’t just automate deployments. It automates trust validation.
Why Security Became a Core Software Delivery Requirement
Traditional perimeter-based security models don’t work well in cloud-native environments.
Modern software systems rely on:
- Kubernetes clusters
- Multi-cloud infrastructure
- APIs
- Microservices
- Third-party SaaS integrations
- Open-source dependencies
- Distributed development teams
- Continuous deployments
Every one of those components expands the attack surface.
Several trends accelerated the move toward DevSecOps:
Open-Source Dependency Risks
Most modern applications rely heavily on open-source packages. A single vulnerable library can expose entire production systems.
Incidents involving Log4Shell and SolarWinds showed how supply chain vulnerabilities can spread rapidly across organizations.
Faster Release Cycles
Daily deployments leave little room for slow manual security reviews.
Security controls must operate continuously and automatically.
Cloud Misconfiguration Risks
Cloud infrastructure introduced new attack vectors:
- Public S3 buckets
- Misconfigured IAM policies
- Exposed Kubernetes dashboards
- Overprivileged service accounts
- Unsecured APIs
Many breaches now originate from configuration weaknesses rather than traditional software exploits.
Regulatory Pressure
Frameworks like:
- SOC 2
- HIPAA
- PCI DSS
- ISO 27001
- GDPR
require stronger auditability and security controls throughout software delivery pipelines.
DevSecOps vs DevOps: Core Differences
Security Ownership
Traditional DevOps
Security responsibility often belongs to a dedicated security team.
Developers focus primarily on functionality and deployment speed.
Security reviews happen separately from development workflows.
DevSecOps
Security becomes a shared responsibility across:
- Developers
- Operations engineers
- Platform teams
- Security engineers
- Compliance teams
Security controls integrate directly into development pipelines.
Pipeline Architecture
Traditional DevOps
Pipelines mainly focus on:
- Build automation
- Testing
- Deployment
- Monitoring
Security validation may occur after deployment.
DevSecOps
Pipelines include integrated security gates such as:
- SAST scans
- Dependency checks
- Container image scanning
- IaC validation
- Secret detection
- Runtime policy enforcement
Security testing becomes continuous.
Vulnerability Detection Timing
Traditional DevOps
Issues are often detected late:
- Pre-release testing
- Post-deployment audits
- External penetration tests
Late detection increases remediation costs.
DevSecOps
Security flaws are identified earlier:
- During coding
- During pull requests
- During builds
- During infrastructure provisioning
Earlier detection reduces risk exposure dramatically.
Automation Scope
Traditional DevOps
Automation focuses primarily on operational efficiency.
DevSecOps
Automation extends to:
- Threat detection
- Policy enforcement
- Compliance validation
- Security scanning
- Runtime protection
Security becomes programmable.
Comparing Security Responsibilities Across Teams
One of the biggest operational differences between DevSecOps and traditional DevOps is how organizations distribute responsibility.
Traditional Security Workflow
A typical traditional workflow might look like this:
- Developers write code
- DevOps deploys applications
- Security team reviews releases later
- Vulnerabilities are reported back
- Developers fix issues retroactively
This creates friction because security becomes a bottleneck.
DevSecOps Workflow
DevSecOps restructures the process:
- Developers receive immediate security feedback
- Automated scans run inside CI/CD pipelines
- Infrastructure policies are validated automatically
- Secrets are detected before commits
- Security baselines are enforced continuously
Security shifts from reactive to proactive.
CI/CD Security in DevSecOps Pipelines
CI/CD security is one of the most important distinctions between DevOps and DevSecOps.
Traditional pipelines prioritize deployment speed.
DevSecOps pipelines prioritize both speed and trust verification.
Key Security Controls in DevSecOps Pipelines
Static Application Security Testing (SAST)
SAST tools analyze source code for vulnerabilities before applications run.
Common detections include:
- SQL injection risks
- Hardcoded credentials
- Unsafe deserialization
- Buffer overflows
- Authentication weaknesses
Popular tools include:
- SonarQube
- Semgrep
- Checkmarx
- Veracode
Dynamic Application Security Testing (DAST)
DAST tools test running applications from the outside.
They simulate attacker behavior against deployed environments.
DAST commonly identifies:
- Broken authentication
- API vulnerabilities
- Session management flaws
- Cross-site scripting (XSS)
Software Composition Analysis (SCA)
SCA tools analyze open-source dependencies for known vulnerabilities.
This is critical because modern applications may contain hundreds or thousands of third-party libraries.
Tools include:
- Snyk
- Dependabot
- Mend
- Black Duck
Infrastructure as Code Scanning
IaC security tools inspect Terraform, CloudFormation, and Kubernetes manifests.
Common issues include:
- Open network ports
- Weak IAM permissions
- Public storage exposure
- Missing encryption settings
Popular platforms include:
- Checkov
- tfsec
- Terrascan
Container Security
Containerized applications introduced new risks involving:
- Vulnerable base images
- Privilege escalation
- Unsafe runtime permissions
- Insecure registries
DevSecOps environments often integrate:
- Image scanning
- Runtime container monitoring
- Admission controllers
- Kubernetes policy enforcement
Application Security Testing in Modern Delivery Workflows
Application security testing is no longer an isolated event.
In DevSecOps, testing becomes continuous and layered.
Common Testing Layers
Pre-Commit Security Checks
Developers receive alerts before code even reaches the repository.
Examples include:
- Secret scanning
- Dependency validation
- Git hook enforcement
Pull Request Security Validation
Automated tools analyze proposed changes before merging.
Security findings appear directly inside code review workflows.
Build-Time Security Analysis
Security tools execute during CI builds.
Builds may fail automatically if critical vulnerabilities appear.
Runtime Monitoring
Production systems continue monitoring for:
- Abnormal behavior
- Exploit attempts
- Container drift
- Privilege escalation
- Unauthorized access
This continuous feedback loop is a defining DevSecOps characteristic.
Shift-Left Security Explained
“Shift left” is one of the most widely discussed DevSecOps concepts.
It means moving security earlier into development workflows.
Instead of discovering vulnerabilities after deployment, teams identify issues during:
- Coding
- Pull requests
- Unit testing
- Build pipelines
- Infrastructure provisioning
Why Shift Left Matters
Security flaws become more expensive later in the lifecycle.
Fixing a vulnerability during development may take minutes.
Fixing it in production may involve:
- Emergency patches
- Downtime
- Incident response
- Customer communication
- Compliance reporting
- Reputation damage
Shift-left security reduces both operational risk and financial exposure.
Infrastructure as Code and Cloud Security
Cloud-native architectures transformed infrastructure management.
Infrastructure is now provisioned programmatically using:
- Terraform
- Pulumi
- AWS CloudFormation
- Kubernetes manifests
That creates both opportunities and risks.
Traditional DevOps Infrastructure Risks
Traditional DevOps teams often prioritize deployment automation over policy validation.
Misconfigurations can spread rapidly across environments.
Examples include:
- Public databases
- Overprivileged IAM roles
- Unencrypted storage
- Weak network segmentation
DevSecOps Infrastructure Protection
DevSecOps introduces policy enforcement into infrastructure pipelines.
Examples include:
- IaC scanning
- Kubernetes admission policies
- Cloud compliance validation
- Drift detection
- Runtime policy engines
Security policies become codified and repeatable.
Secrets Management and Identity Controls
Hardcoded credentials remain one of the most common security failures in software systems.
DevSecOps environments address this aggressively.
Common Secrets Risks
- API keys committed to Git
- Shared credentials
- Long-lived tokens
- Weak rotation policies
- Unencrypted environment variables
DevSecOps Secrets Management Practices
Modern DevSecOps platforms use:
- Centralized secret vaults
- Dynamic credential generation
- Short-lived tokens
- Identity federation
- Role-based access control (RBAC)
Common tools include:
- HashiCorp Vault
- AWS Secrets Manager
- Azure Key Vault
- Doppler
Compliance, Governance, and Auditability
Compliance requirements increasingly affect software delivery architecture.
Traditional security approaches often rely on manual evidence collection.
That becomes unsustainable at scale.
DevSecOps Compliance Automation
DevSecOps improves audit readiness through automation.
Examples include:
- Immutable deployment logs
- Automated policy validation
- Continuous compliance checks
- Infrastructure version tracking
- Security event monitoring
This is especially valuable for SaaS companies pursuing:
- SOC 2 certification
- HIPAA compliance
- PCI DSS validation
- ISO 27001 controls
Automation in DevSecOps
Automation is where DevSecOps becomes operationally scalable.
Without automation, secure delivery pipelines become too slow.
Areas Commonly Automated
Security Scanning
Automated scans run during:
- Commits
- Pull requests
- CI builds
- Container builds
- Deployments
Policy Enforcement
Rules can automatically block:
- Insecure configurations
- Exposed secrets
- Vulnerable dependencies
- Non-compliant infrastructure
Incident Detection
Monitoring systems identify:
- Suspicious runtime activity
- Unauthorized access
- Configuration drift
- Anomalous API behavior
Threat Modeling and Risk Reduction
Traditional DevOps environments often lack structured threat analysis.
DevSecOps encourages proactive risk modeling.
Threat Modeling Questions
Teams analyze:
- What assets are sensitive?
- What attack vectors exist?
- Which APIs expose risk?
- What privilege boundaries exist?
- What happens if credentials leak?
Threat modeling helps engineering teams build security awareness earlier in development.
Incident Response Differences
Security incidents expose major differences between DevOps and DevSecOps maturity.
Traditional DevOps Incident Handling
Teams often react manually:
- Security discovers breach
- Operations investigate logs
- Developers patch vulnerabilities
- Incident reviews happen afterward
This can be slow and fragmented.
DevSecOps Incident Handling
DevSecOps environments integrate:
- Centralized telemetry
- Runtime monitoring
- Automated alerting
- Security orchestration
- Immutable infrastructure
- Faster rollback mechanisms
Response times improve significantly.
DevSecOps Toolchain Comparison
Traditional DevOps Tooling
Typical stacks may include:
- Jenkins
- GitLab CI
- Docker
- Kubernetes
- Terraform
- Prometheus
Security tooling is often separate.
DevSecOps Tooling
DevSecOps integrates additional security-focused platforms:
| Category | Common Tools |
|---|---|
| SAST | Semgrep, SonarQube |
| DAST | OWASP ZAP, Burp Suite |
| SCA | Snyk, Dependabot |
| IaC Security | Checkov, tfsec |
| Container Security | Trivy, Aqua Security |
| Secrets Management | Vault, AWS Secrets Manager |
| SIEM | Splunk, Elastic Security |
The important shift isn’t just tooling. It’s orchestration.
Security tooling becomes embedded inside delivery workflows instead of existing independently.
Advantages of DevSecOps Over Traditional DevOps
Faster Vulnerability Detection
Early detection reduces remediation cost and operational risk.
Improved Compliance Readiness
Automated evidence collection simplifies audits.
Reduced Attack Surface
Continuous scanning minimizes exposed weaknesses.
Better Developer Awareness
Developers gain direct visibility into security risks.
Safer CI/CD Pipelines
Security validation becomes part of deployment logic.
Stronger Cloud Security
Infrastructure policies become standardized and repeatable.
Common DevSecOps Challenges
Despite the benefits, DevSecOps implementation isn’t simple.
Toolchain Complexity
Too many disconnected security tools can overwhelm teams.
Alert fatigue becomes a serious issue.
Developer Resistance
Some developers initially view security gates as productivity blockers.
Poorly implemented security workflows can slow delivery velocity.
False Positives
Security scanners sometimes generate noisy findings.
Teams need proper tuning and prioritization.
Skills Gaps
Organizations often struggle to hire engineers who understand:
- Cloud infrastructure
- Secure coding
- Kubernetes security
- Compliance automation
- CI/CD architecture
Cultural Change
DevSecOps requires cross-functional collaboration.
That cultural transition is often harder than the technical implementation.
Real-World SaaS and Enterprise Use Cases
SaaS Platforms
SaaS companies deploy frequently and manage sensitive customer data.
DevSecOps helps them:
- Secure APIs
- Prevent secrets exposure
- Maintain SOC 2 compliance
- Monitor multi-tenant infrastructure
- Reduce dependency risks
Fintech Systems
Financial applications face strict regulatory requirements.
DevSecOps enables:
- Continuous compliance validation
- Secure transaction pipelines
- Automated audit trails
- Faster patch management
Healthcare Platforms
Healthcare systems must protect patient information under HIPAA requirements.
DevSecOps improves:
- Access control enforcement
- Encryption validation
- Infrastructure auditability
- Secure cloud deployments
Enterprise Cloud Migration
Large enterprises modernizing legacy infrastructure use DevSecOps to:
- Standardize cloud governance
- Reduce misconfigurations
- Automate policy enforcement
- Improve visibility across hybrid environments
DevSecOps Adoption Strategy
Organizations rarely transition overnight.
Successful adoption usually happens incrementally.
Step 1: Start With Visibility
Implement:
- Dependency scanning
- Secret detection
- CI pipeline logging
Gain visibility before enforcing hard policies.
Step 2: Integrate Security Into CI/CD
Add:
- SAST
- SCA
- Container scanning
- IaC validation
inside pipelines.
Step 3: Standardize Policies
Create reusable security baselines.
Examples include:
- Approved container images
- Secure Terraform modules
- RBAC standards
Step 4: Automate Enforcement
Block deployments that violate critical policies.
Use severity thresholds to reduce noise.
Step 5: Improve Runtime Security
Add:
- Runtime monitoring
- SIEM integration
- Threat detection
- Behavioral analytics
Common Misconceptions About DevSecOps
“DevSecOps Slows Down Development”
Poor implementation slows development.
Well-designed DevSecOps improves delivery stability and reduces emergency remediation work.
“Security Teams Become Unnecessary”
Security expertise becomes even more important.
The difference is that security integrates into engineering workflows instead of operating separately.
“Buying Security Tools Equals DevSecOps”
Tools alone don’t create secure pipelines.
Processes, culture, automation, and governance matter just as much.
“Only Large Enterprises Need DevSecOps”
Startups are increasingly targeted because they often lack mature security controls.
Even small SaaS platforms benefit from secure development pipelines.
Future Trends in Secure Software Delivery
DevSecOps continues evolving rapidly.
Several trends are shaping the future.
AI-Assisted Security Analysis
AI-powered tools increasingly help:
- Detect anomalous behavior
- Identify insecure code patterns
- Prioritize vulnerabilities
- Reduce false positives
Software Supply Chain Security
Supply chain protection is becoming a major focus area.
Organizations are adopting:
- SBOMs (Software Bills of Materials)
- Artifact signing
- Provenance verification
- Dependency attestation
Policy-as-Code
Security policies are becoming machine-readable and enforceable automatically across infrastructure and deployment systems.
Zero Trust Architectures
Modern DevSecOps environments increasingly integrate:
- Continuous identity verification
- Least-privilege enforcement
- Segmented workloads
- Context-aware authentication
FAQ Section
What is the biggest difference between DevOps and DevSecOps?
The biggest difference is security integration.
Traditional DevOps prioritizes delivery speed and operational collaboration, while DevSecOps embeds automated security controls throughout the software delivery lifecycle.
Does DevSecOps replace DevOps?
No.
DevSecOps extends DevOps principles by adding integrated security practices.
It builds on DevOps rather than replacing it.
Why is DevSecOps important for CI/CD pipelines?
CI/CD pipelines deploy software rapidly and continuously.
Without integrated security controls, vulnerabilities can reach production environments much faster.
DevSecOps introduces automated validation that reduces this risk.
What tools are commonly used in DevSecOps?
Popular DevSecOps tools include:
GitHub Advanced Security
Snyk
SonarQube
Semgrep
Trivy
Checkov
HashiCorp Vault
Aqua Security
Is DevSecOps only for cloud-native applications?
No.
Although DevSecOps is heavily associated with cloud-native systems, its principles apply to:
On-premise applications
Hybrid infrastructure
Legacy modernization projects
Enterprise software systems
What is shift-left security?
Shift-left security means identifying vulnerabilities earlier in the development lifecycle instead of waiting until production or late-stage testing.
Can small startups implement DevSecOps?
Yes.
Even lightweight practices like dependency scanning, secret detection, and automated security checks significantly improve security posture for startups.
What role does Kubernetes play in DevSecOps?
Kubernetes introduces orchestration flexibility but also increases infrastructure complexity.
DevSecOps practices help secure Kubernetes environments through policy enforcement, workload isolation, image scanning, and runtime monitoring.
Conclusion
The difference between DevSecOps and traditional DevOps goes far beyond adding a few security tools to a CI/CD pipeline.
It represents a fundamental shift in how software organizations think about risk, automation, accountability, and delivery architecture.
Traditional DevOps optimized for speed and operational efficiency. DevSecOps optimizes for speed with continuous trust validation.
That distinction matters more than ever.
Modern software environments are deeply interconnected. APIs, containers, cloud infrastructure, open-source dependencies, and distributed systems all expand the attack surface. Security can no longer operate as a disconnected approval stage.
Organizations adopting DevSecOps gain earlier vulnerability detection, stronger compliance readiness, improved deployment confidence, and better resilience against evolving threats.
The most successful teams understand something important: secure software delivery is no longer just a security objective. It’s a core engineering capability.