How Compliance Automation Simplifies Enterprise Security Operations
Enterprise security teams are under pressure from every direction. Threat surfaces keep expanding, regulations change constantly, cloud infrastructure evolves weekly, and auditors still expect detailed evidence delivered on demand.
A few years ago, many organizations could survive with spreadsheets, screenshots, ticket exports, and quarterly compliance reviews. That approach is now collapsing under the weight of modern infrastructure.
Today’s enterprise environments include:
- Multi-cloud deployments
- Remote work infrastructure
- SaaS ecosystems
- Third-party integrations
- Containerized workloads
- Identity platforms
- Continuous software delivery pipelines
- Hybrid data storage systems
Every one of those systems generates security obligations, policy requirements, access controls, and audit evidence.
That’s where compliance automation changes the game.
Instead of treating compliance as a slow, manual process that interrupts security operations, automation turns governance into an ongoing operational layer integrated directly into enterprise infrastructure. Security teams gain continuous visibility. Compliance managers reduce repetitive administrative work. Auditors receive cleaner evidence. Leadership gets measurable risk insights.
The result isn’t just faster compliance. It’s a more resilient and scalable security operation.
What Compliance Automation Actually Means
Compliance automation refers to the use of software, workflows, integrations, and policy-driven systems to manage regulatory requirements, security controls, governance tasks, evidence collection, and audit preparation with minimal manual effort.
At a practical level, compliance automation platforms continuously monitor systems, evaluate controls, and collect evidence automatically.
Instead of asking teams to manually verify:
- Access permissions
- Encryption status
- Configuration policies
- Security patch levels
- Vendor compliance
- User activity logs
- Incident response documentation
…the platform performs those checks continuously.
This shifts compliance from a reactive audit exercise into an operational security function.
Manual Compliance vs Automated Compliance
Manual Approach
Traditional enterprise compliance processes often involve:
- Spreadsheet tracking
- Email approvals
- Screenshot evidence
- Periodic access reviews
- Human-driven policy validation
- Separate audit preparation cycles
- Disconnected governance systems
These processes are slow, inconsistent, and difficult to scale.
Automated Approach
Automated compliance workflows centralize and standardize these tasks through:
- Policy engines
- Security orchestration
- API integrations
- Cloud monitoring
- Identity governance
- Continuous control assessments
- Automated reporting
Instead of scrambling before an audit, organizations maintain ongoing compliance readiness.
The Growing Complexity of Enterprise Security Compliance
Modern enterprises rarely operate under a single framework.
A healthcare organization may simultaneously manage:
- HIPAA
- SOC 2
- ISO 27001
- GDPR
- PCI DSS
- Internal governance policies
- Regional data residency requirements
Meanwhile, a financial enterprise may face:
- SOX
- GLBA
- NIST requirements
- Cyber insurance obligations
- Vendor security mandates
Each framework contains overlapping controls, but implementation details vary.
Without automation, teams end up duplicating work across multiple governance systems.
Why Traditional Processes Fail at Scale
Manual compliance operations introduce several operational problems.
Evidence Collection Bottlenecks
Audits often require evidence from dozens of systems:
- SIEM platforms
- IAM providers
- Endpoint management tools
- Cloud providers
- HR systems
- Ticketing systems
- Vulnerability scanners
Pulling that evidence manually creates delays and inconsistencies.
Human Error
Manual workflows increase the likelihood of:
- Missing evidence
- Incorrect documentation
- Inconsistent policy enforcement
- Outdated controls
- Forgotten reviews
Even experienced compliance teams struggle when environments grow rapidly.
Audit Fatigue
Security engineers frequently complain that compliance work distracts from actual security improvement.
Teams spend time:
- Exporting logs
- Taking screenshots
- Filling spreadsheets
- Updating documents
- Responding to repetitive auditor requests
Automation reduces this operational drag significantly.
Core Components of Automated Compliance Workflows
Compliance automation platforms typically combine several operational capabilities.
Continuous Monitoring
Continuous monitoring tracks security controls in real time instead of relying on periodic assessments.
Examples include:
- Detecting disabled MFA policies
- Monitoring encryption settings
- Identifying unpatched assets
- Tracking privileged account changes
- Reviewing access anomalies
This allows organizations to identify compliance drift quickly.
Automated Evidence Collection
One of the biggest operational advantages is automated evidence gathering.
Instead of manually collecting proof for auditors, systems automatically archive:
- Configuration states
- Access logs
- Security policies
- Approval records
- Incident response documentation
- Vulnerability remediation timelines
This dramatically shortens audit preparation cycles.
Policy Enforcement
Governance automation platforms can enforce security policies automatically.
For example:
- Blocking non-compliant cloud deployments
- Preventing public storage exposure
- Enforcing password standards
- Restricting unauthorized software installations
- Requiring encryption by default
This reduces the gap between written policy and operational reality.
Workflow Orchestration
Automated compliance workflows often integrate with:
- ITSM platforms
- Identity systems
- CI/CD pipelines
- Ticketing tools
- Security orchestration systems
That integration enables:
- Automated approvals
- Escalation workflows
- Remediation assignments
- Risk notifications
- Policy review scheduling
How Compliance Automation Improves Enterprise Security Operations
The biggest misconception about compliance automation is that it only helps auditors.
In reality, automation strengthens operational cybersecurity itself.
Faster Threat Detection
Continuous monitoring surfaces configuration drift and risky changes quickly.
For example:
- Disabled logging
- Open firewall ports
- Excessive user privileges
- Missing endpoint protection
- Unencrypted storage
These issues affect both compliance posture and real security risk.
Better Incident Response
Automated governance systems improve response coordination by:
- Tracking remediation tasks
- Logging response actions
- Maintaining evidence trails
- Preserving forensic data
- Standardizing escalation paths
This improves operational consistency during security incidents.
Reduced Security Team Burnout
Security teams already face alert fatigue and staffing shortages.
Removing repetitive compliance work frees engineers to focus on:
- Threat hunting
- Architecture improvements
- Detection engineering
- Vulnerability management
- Strategic risk reduction
That operational shift has major long-term value.
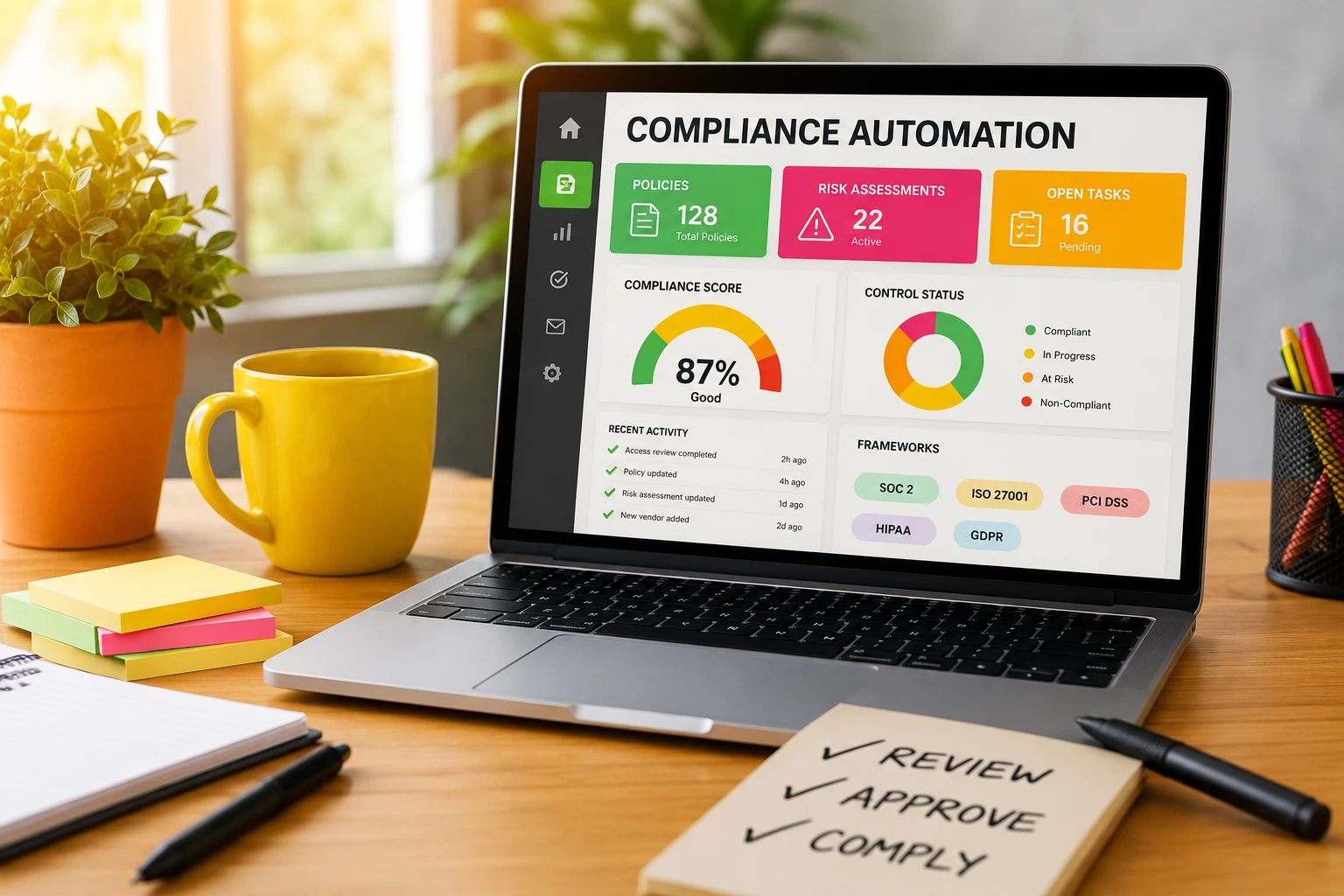
Stronger Executive Visibility
Enterprise leadership increasingly wants measurable security metrics.
Compliance automation platforms provide dashboards covering:
- Control coverage
- Risk exposure
- Policy violations
- Audit readiness
- Vendor compliance status
- Remediation progress
This helps CISOs communicate operational risk more effectively.
Governance Automation and Risk Visibility
Governance automation extends beyond compliance checklists.
It creates centralized operational visibility across enterprise risk environments.
Centralized Control Mapping
Modern governance platforms map controls across multiple frameworks simultaneously.
For example:
A single MFA policy may satisfy requirements related to:
- SOC 2
- ISO 27001
- HIPAA
- PCI DSS
- NIST
Without automation, teams often manage these separately.
Control mapping reduces duplication dramatically.
Continuous Risk Scoring
Some advanced platforms calculate risk dynamically using:
- Asset exposure
- Vulnerability severity
- Identity risk
- Misconfiguration trends
- Vendor assessment results
This helps organizations prioritize remediation more intelligently.
Third-Party Risk Management
Vendor ecosystems are now one of the biggest enterprise security concerns.
Governance automation platforms can streamline:
- Vendor onboarding
- Security questionnaires
- Evidence requests
- Contract reviews
- Continuous vendor monitoring
This is especially important for enterprises operating in regulated industries.
Real-World Use Cases Across Enterprise Environments
Compliance automation affects nearly every modern enterprise environment.
Cloud Infrastructure Compliance
Cloud environments change rapidly.
Automation helps monitor:
- AWS IAM policies
- Azure configurations
- Google Cloud permissions
- Storage exposure
- Kubernetes security settings
- Container compliance
Manual oversight simply cannot keep pace with cloud velocity.
DevSecOps Integration
Compliance automation increasingly integrates directly into software delivery pipelines.
Examples include:
- Automated code scanning
- Policy checks during deployment
- Infrastructure-as-code validation
- Container image scanning
- Secret detection
- Dependency compliance verification
This shifts governance earlier into the development lifecycle.
Identity and Access Governance
Identity remains a central compliance focus.
Automation helps manage:
- User provisioning
- Role-based access controls
- Privileged account reviews
- MFA enforcement
- Access certifications
- Termination workflows
This reduces insider risk and audit exposure.
Healthcare Compliance Operations
Healthcare organizations handle massive volumes of sensitive data.
Automation assists with:
- HIPAA safeguards
- Access logging
- PHI monitoring
- Device compliance
- Audit trail retention
- Incident documentation
Healthcare compliance environments especially benefit from continuous monitoring.
Financial Services Governance
Banks and fintech organizations operate under strict regulatory scrutiny.
Automation improves:
- Transaction monitoring
- Change management
- Segregation of duties
- Audit logging
- Data retention
- Security reporting
These environments require extremely consistent governance controls.
Regulatory Frameworks Commonly Managed Through Automation
Most compliance automation programs support multiple frameworks simultaneously.
SOC 2
Automation simplifies:
- Access reviews
- Change tracking
- Evidence management
- Control monitoring
- Vendor oversight
SOC 2 readiness becomes significantly easier when evidence collection is continuous.
ISO 27001
Governance automation helps organizations maintain:
- Asset inventories
- Risk registers
- Policy management
- Security control monitoring
- Internal audit preparation
HIPAA
Healthcare organizations use automation for:
- Access auditing
- Security monitoring
- Documentation management
- Incident reporting
- Administrative safeguard enforcement
PCI DSS
Payment environments require continuous oversight.
Automation supports:
- Cardholder data monitoring
- Network segmentation verification
- Vulnerability tracking
- Log retention
- Access control enforcement
GDPR
Privacy-focused compliance programs use automation to manage:
- Data processing records
- Consent management
- Access requests
- Retention policies
- Cross-border transfer governance
Benefits Beyond Audit Preparation
Audit readiness is important, but automation creates broader operational value.
Faster Scaling
As enterprises grow, manual compliance processes become operational bottlenecks.
Automation allows organizations to scale governance without increasing headcount proportionally.
Improved Consistency
Automation standardizes workflows across departments, regions, and business units.
This reduces governance fragmentation.
Better Data Accuracy
Automated systems reduce reporting inconsistencies caused by manual entry errors.
That improves both compliance reliability and executive decision-making.
Continuous Readiness
Organizations no longer need massive audit preparation projects every quarter.
Instead, they maintain ongoing compliance visibility.
Common Challenges and Misconceptions
Compliance automation is powerful, but implementation isn’t effortless.
Misconception: Automation Eliminates Human Oversight
Automation reduces repetitive tasks, but governance still requires:
- Policy decisions
- Risk assessments
- Executive approvals
- Exception handling
- Strategic oversight
Human expertise remains essential.
Integration Complexity
Large enterprises often operate fragmented technology stacks.
Integrating:
- Legacy systems
- Cloud environments
- Security tools
- HR systems
- Identity platforms
…can take time.
Strong API support becomes critical.
Poor Policy Design
Automation cannot fix weak governance structures.
If policies are unclear or inconsistent, automation may simply scale operational confusion faster.
Alert Overload
Some organizations overconfigure monitoring systems and generate excessive compliance alerts.
That creates operational fatigue.
Successful programs prioritize meaningful signals instead of monitoring everything equally.
How to Implement Compliance Automation Successfully
The most effective implementations follow a phased operational strategy.
Start With High-Impact Areas
Most enterprises begin with:
- Access management
- Evidence collection
- Cloud configuration monitoring
- Vulnerability compliance
- Policy tracking
These areas usually deliver quick operational wins.
Map Existing Controls
Before automating workflows, organizations should inventory:
- Existing controls
- Compliance obligations
- Security processes
- Reporting requirements
- Audit dependencies
This prevents duplicate automation efforts.
Integrate Security and Compliance Teams
Many enterprises still separate governance and security operations.
That silo creates friction.
Automation initiatives work best when:
- Compliance teams
- Security engineers
- IT operations
- Legal teams
- Risk management
…collaborate early.
Build Continuous Processes
The goal isn’t annual audit preparation.
The goal is continuous operational governance.
That mindset shift changes how organizations approach compliance maturity.
Compliance Automation Tools and Technology Stack
Enterprise compliance automation typically involves multiple integrated technologies.
Governance, Risk, and Compliance Platforms
GRC systems centralize:
- Policies
- Controls
- Risk registers
- Audit workflows
- Evidence repositories
SIEM Platforms
Security Information and Event Management systems provide:
- Log analysis
- Threat monitoring
- Compliance reporting
- Event correlation
CSPM Solutions
Cloud Security Posture Management tools monitor:
- Cloud misconfigurations
- Identity risks
- Compliance drift
- Infrastructure exposure
Identity Governance Platforms
Identity systems automate:
- User lifecycle management
- Access reviews
- Privileged access controls
- Authentication policies
Workflow Automation Platforms
Operational workflow systems connect governance tasks across departments.
This reduces manual coordination overhead.
Metrics Enterprises Should Track
Effective governance automation programs rely on measurable operational metrics.
Mean Time to Remediate Compliance Issues
This measures how quickly teams resolve policy violations or control failures.
Audit Preparation Time
Automation should significantly reduce audit readiness cycles.
Control Coverage Percentage
Organizations should track how many controls are continuously monitored versus manually validated.
Policy Violation Trends
Monitoring recurring violations helps identify systemic weaknesses.
Evidence Collection Efficiency
Enterprises should measure reductions in manual evidence gathering workloads.
Future Trends in Governance and Regulatory Automation
Compliance automation continues evolving rapidly.
Several major trends are shaping enterprise adoption.
AI-Assisted Compliance Analysis
Artificial intelligence increasingly helps organizations:
- Analyze policy gaps
- Detect anomalies
- Recommend remediation steps
- Classify risks
- Summarize audit evidence
However, human oversight remains essential for governance decisions.
Continuous Compliance Models
Instead of point-in-time audits, regulators increasingly favor continuous assurance models.
Automation makes this operationally feasible.
Deeper DevSecOps Integration
Compliance checks are moving directly into:
- CI/CD pipelines
- Infrastructure provisioning
- Runtime monitoring
- Application deployment workflows
This reduces late-stage remediation costs.
Unified Security and Governance Platforms
Vendors increasingly combine:
- Security operations
- Risk management
- Compliance monitoring
- Identity governance
- Threat detection
…into consolidated operational platforms.
FAQ
What is compliance automation in cybersecurity?
Compliance automation uses software and workflow systems to automate security controls, evidence collection, governance processes, and regulatory monitoring within enterprise environments.
How does automated compliance improve security operations?
Automated compliance improves visibility, reduces manual tasks, speeds up remediation, standardizes governance workflows, and enables continuous monitoring across enterprise infrastructure.
Which industries benefit most from compliance automation?
Highly regulated industries benefit the most, including:
Healthcare
Financial services
SaaS providers
Government contractors
E-commerce
Manufacturing
Enterprise technology companies
Can compliance automation reduce audit costs?
Yes. Automation reduces manual evidence collection, shortens preparation cycles, and improves reporting accuracy, which often lowers audit overhead.
Is compliance automation only for large enterprises?
No. Mid-sized organizations increasingly adopt governance automation as cloud environments and regulatory obligations grow more complex.
What are common compliance automation tools?
Common categories include:
GRC platforms
SIEM systems
CSPM tools
Identity governance solutions
Workflow orchestration platforms
Security automation platforms
Does automation replace compliance teams?
No. Automation supports compliance professionals by reducing repetitive operational tasks, but governance strategy and risk management still require human oversight.
Conclusion
Enterprise compliance is no longer just an audit problem. It’s an operational scalability problem tied directly to cybersecurity resilience, governance maturity, and organizational risk visibility.
Manual processes cannot keep pace with modern infrastructure complexity. Cloud environments change too quickly. Regulatory obligations overlap constantly. Security teams are already overloaded.
Compliance automation helps enterprises move from reactive governance to continuous operational assurance.
The biggest value isn’t simply faster audits. It’s stronger visibility, more consistent policy enforcement, reduced operational friction, and better alignment between security operations and regulatory requirements.
Organizations that successfully integrate automated compliance workflows into their broader security architecture gain something increasingly important in modern enterprise environments: sustainable governance at scale.