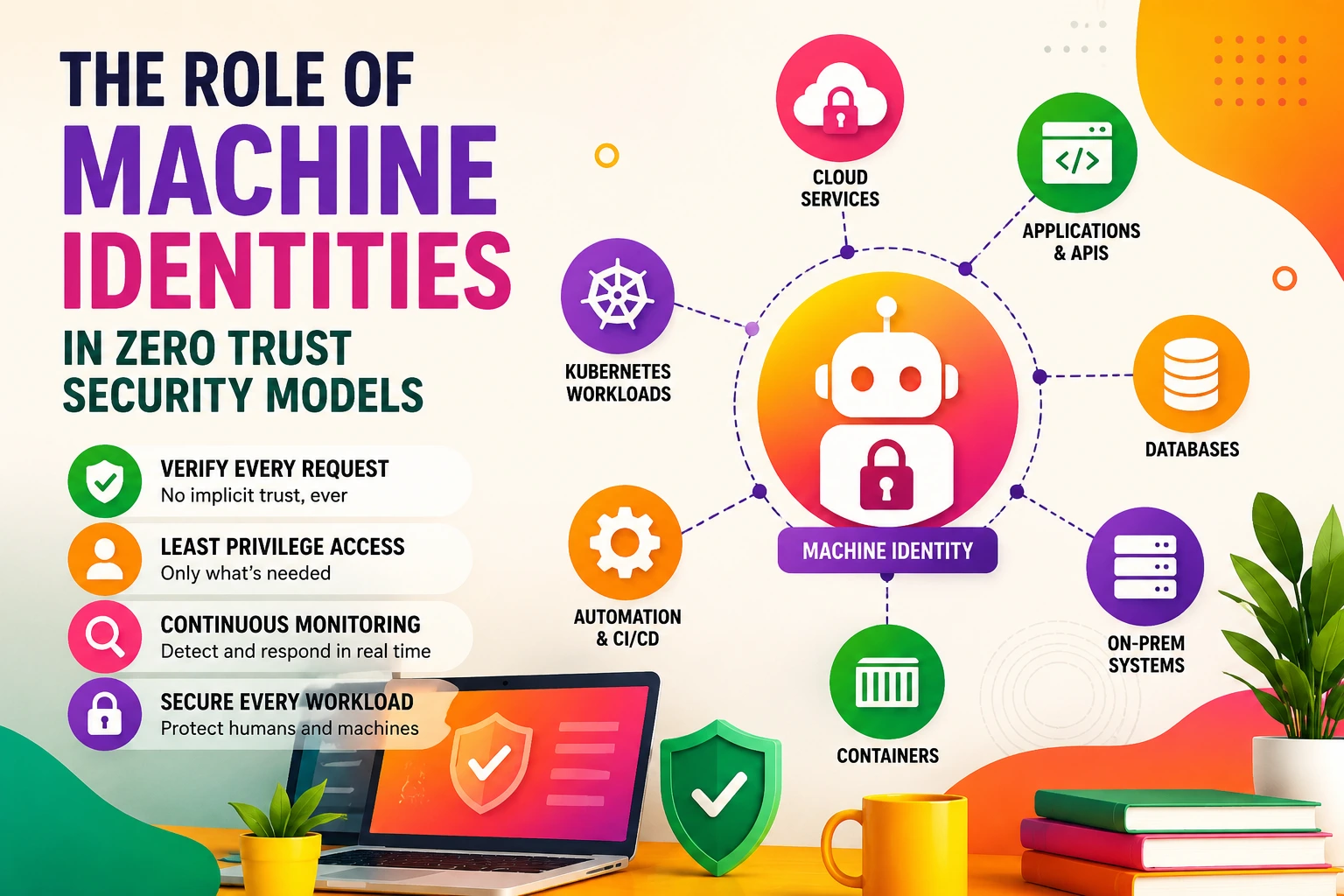
The Role of Machine Identities in Zero Trust Security Models
Modern infrastructure no longer revolves around employees sitting behind corporate firewalls. Today’s enterprise environments run on APIs, containers, microservices, CI/CD pipelines, serverless workloads, edge systems, and automated cloud services talking to each other constantly.
And every one of those interactions requires trust.
That’s where machine identities enter the picture.
For many organizations, non-human identities now outnumber human users by massive margins. A single Kubernetes cluster can generate thousands of short-lived workload identities. Cloud-native applications rely on automated authentication between services every second. Infrastructure automation tools, AI workloads, and DevOps pipelines all require secure identity verification.
The problem? Most security programs were originally designed around people, not machines.
Attackers know this.
Instead of targeting employees directly, threat actors increasingly target service accounts, API keys, OAuth tokens, SSH keys, certificates, and unmanaged workloads because they often provide broad access with limited monitoring. In many environments, machine identities have become the fastest-growing attack surface in cybersecurity.
At the same time, enterprises are moving toward zero trust security models where nothing is trusted implicitly — not users, devices, applications, or workloads.
Zero trust changes the rules entirely.
Every request must be authenticated, verified, authorized, and continuously evaluated. That philosophy applies just as much to machines as it does to humans.
Machine identity security is now foundational infrastructure.
Without strong machine authentication, zero trust architectures simply collapse.
This article explores how machine identities work, why they matter in cloud infrastructure, how they integrate with zero trust frameworks, and what security teams need to do to protect them at scale.
What Are Machine Identities?
A machine identity is a digital credential used by software, devices, services, workloads, or infrastructure components to authenticate themselves within a system.
Think of machine identities as the equivalent of usernames and passwords for non-human entities.
But in practice, they’re far more complex.
Machine identities can include:
- TLS certificates
- API keys
- OAuth tokens
- SSH keys
- Kubernetes service accounts
- Cloud IAM roles
- SPIFFE identities
- Workload tokens
- Code signing certificates
- Device certificates
These identities allow systems to verify:
- Who or what is making a request
- Whether the entity is trusted
- What permissions it should have
- Whether access should continue
Without machine authentication, encrypted communication and secure automation become impossible.
In cloud-native environments, machine identities are everywhere.
A microservice calling another microservice uses a machine identity.
A CI/CD pipeline deploying infrastructure uses a machine identity.
A Kubernetes pod communicating with a database uses a machine identity.
An API gateway validating backend services uses machine authentication.
The scale becomes enormous very quickly.
Large enterprises may manage millions of machine identities across multi-cloud environments.
Human vs Non-Human Identities
Traditional identity and access management focused primarily on employees and contractors.
Those systems were built around concepts like:
- Usernames
- Passwords
- MFA
- SSO
- Role-based access
Machine identities operate differently.
Unlike humans, machines:
- Authenticate continuously
- Operate 24/7
- Scale dynamically
- Rotate rapidly
- Often exist temporarily
- Require automated provisioning
A containerized workload might exist for only minutes before being destroyed and recreated.
That creates unique challenges.
Security teams can’t manually manage certificates or credentials at that scale. Automation becomes mandatory.
Non human identity security has evolved into a specialized cybersecurity discipline because conventional IAM practices struggle to handle machine-scale authentication.
Why Zero Trust Depends on Machine Authentication
Zero trust security assumes no entity should be trusted automatically, even inside corporate networks.
Every request requires verification.
That sounds straightforward when discussing employees. But modern infrastructure traffic is dominated by machine-to-machine communication.
In many environments:
- 80–95% of authentication traffic is non-human
- East-west traffic exceeds north-south traffic
- APIs generate most internal communication
- Microservices authenticate constantly
Without machine identity verification, zero trust becomes incomplete.
Here’s why machine authentication is central to zero trust:
Continuous Verification
Zero trust requires continuous authentication rather than one-time validation.
Machine identities enable:
- Mutual TLS authentication
- Token validation
- Service attestation
- Dynamic trust evaluation
Every workload must prove its identity repeatedly.
Least Privilege Enforcement
Zero trust architectures rely heavily on least privilege access.
Machine identities make it possible to define:
- Granular workload permissions
- Service-specific access rules
- Context-aware authorization
- Temporary credentials
Instead of broad network trust, access becomes identity-driven.
Microsegmentation
Modern zero trust environments use microsegmentation to isolate workloads.
Machine identity systems help enforce segmentation by validating:
- Service identity
- Workload integrity
- Communication permissions
- Policy compliance
Without verified workload identities, segmentation policies lose effectiveness.
Secure Automation
Cloud infrastructure depends on automation.
Infrastructure-as-code pipelines, orchestration systems, and deployment tools all require secure machine authentication.
Zero trust security must extend into automated systems, not just human users.
Types of Machine Identities in Modern Infrastructure
Machine identities appear in many forms depending on the environment.
TLS Certificates
TLS certificates remain one of the most common machine identity mechanisms.
They provide:
- Encryption
- Authentication
- Trust validation
Mutual TLS (mTLS) allows both client and server to verify each other’s identity.
This has become critical in service mesh architectures.
API Keys
APIs frequently use keys for authentication between systems.
The problem?
API keys are often static, overprivileged, and poorly rotated.
Many breaches now involve exposed API credentials.
OAuth Tokens
Modern cloud-native applications commonly rely on OAuth and OpenID Connect tokens.
These support:
- Delegated authorization
- Short-lived access
- Fine-grained scopes
Token-based machine authentication is increasingly replacing static credentials.
SSH Keys
Infrastructure automation frequently depends on SSH authentication.
Improper SSH key management remains a major enterprise risk because keys are often:
- Shared
- Untracked
- Long-lived
- Overprivileged
Workload Identities
Workload identities are becoming central to cloud security.
These identities are assigned dynamically to workloads such as:
- Containers
- Pods
- Virtual machines
- Serverless functions
Cloud providers increasingly support native workload identity frameworks.
Examples include:
- AWS IAM Roles for Service Accounts
- Google Workload Identity Federation
- Azure Managed Identities
How Machine Identities Work in Cloud Environments
Cloud infrastructure changed identity management dramatically.
Traditional perimeter-based trust models assumed systems inside networks were relatively safe.
Cloud environments destroyed those assumptions.
Infrastructure is now:
- Distributed
- Ephemeral
- API-driven
- Dynamically orchestrated
Machine identities became the replacement for network trust.
Instead of trusting IP addresses or internal subnets, systems trust verified identities.
Here’s a simplified workflow:
- A workload starts
- The orchestration platform assigns an identity
- The workload requests access to another service
- Authentication verifies identity
- Authorization policies evaluate permissions
- Secure communication begins
Everything depends on cryptographic trust.
Workload Identities in Kubernetes and Containers
Kubernetes accelerated the need for scalable machine identity security.
Containers are ephemeral by nature.
Traditional credential management doesn’t work well when workloads constantly spin up and down.
Workload identities solve this problem.
Instead of embedding secrets inside containers, platforms dynamically assign trusted identities at runtime.
That reduces:
- Secret sprawl
- Credential exposure
- Manual key management
- Long-lived credentials
Service meshes like Istio and Linkerd commonly integrate workload identity systems using mutual TLS.
This enables:
- Automatic service authentication
- Encrypted east-west traffic
- Identity-aware policies
- Secure service discovery
In large-scale Kubernetes environments, workload identities are now essential security primitives.
Machine Identity Protection Challenges
Machine identity protection sounds straightforward until scale enters the equation.
Enterprises often manage:
- Millions of certificates
- Thousands of service accounts
- Multi-cloud IAM policies
- Short-lived workloads
- Third-party integrations
That creates major operational complexity.
Visibility Problems
Many organizations lack a complete inventory of machine identities.
Shadow credentials become common.
Security teams may not know:
- Which identities exist
- Who created them
- What permissions they hold
- Whether they’re still active
This creates hidden attack paths.
Credential Sprawl
Developers frequently hardcode credentials into:
- Scripts
- Repositories
- CI/CD pipelines
- Containers
- Configuration files
Even mature organizations struggle with secret sprawl.
Certificate Expiration
Certificate outages can cause major production failures.
Expired certificates have disrupted:
- Banking systems
- Airlines
- Cloud services
- Enterprise applications
Certificate lifecycle management is now a critical operational function.
Excessive Permissions
Machine identities often accumulate broad privileges over time.
Attackers love overprivileged service accounts because they provide lateral movement opportunities.
Common Attack Vectors Targeting Machine Identities
Attackers increasingly focus on machine identity abuse because these credentials often bypass traditional security monitoring.
Stolen API Keys
Public GitHub repositories still expose sensitive credentials regularly.
Attackers scan continuously for:
- Cloud keys
- API secrets
- Tokens
- Certificates
Service Account Abuse
Compromised service accounts can provide persistent access.
Since machine accounts often lack MFA requirements, attackers target them aggressively.
Supply Chain Compromise
Software supply chain attacks frequently involve machine identities.
Compromised CI/CD systems can issue malicious artifacts using trusted credentials.
Certificate Theft
Stolen certificates allow impersonation attacks.
If attackers obtain private keys, they may:
- Intercept encrypted traffic
- Spoof services
- Escalate privileges
Certificates, Secrets, Tokens, and Keys Explained
These concepts often overlap, but they serve different purposes.
Certificates
Used primarily for:
- Identity verification
- Encryption
- Secure communication
Typically based on PKI infrastructure.
Secrets
Broad category including:
- Passwords
- Tokens
- API keys
- Encryption material
Usually stored in secret management systems.
Tokens
Often short-lived authentication artifacts.
Popular in:
- OAuth
- Kubernetes
- Cloud IAM systems
Keys
Cryptographic material used for:
- Signing
- Encryption
- Authentication
Examples include SSH keys and private keys.
IAM, PKI, and SPIFFE in Zero Trust Architectures
Several technologies underpin machine identity security.
Identity and Access Management (IAM)
Cloud IAM systems define:
- Permissions
- Policies
- Trust relationships
- Authentication rules
Major providers include:
- AWS IAM
- Microsoft Entra ID
- Google Cloud IAM
Public Key Infrastructure (PKI)
PKI manages digital certificates and trust chains.
Enterprise PKI environments support:
- Certificate issuance
- Revocation
- Renewal
- Validation
PKI remains foundational for machine authentication.
SPIFFE and SPIRE
SPIFFE (Secure Production Identity Framework for Everyone) has become highly influential in cloud-native security.
SPIFFE standardizes workload identities using cryptographic identity documents.
SPIRE implements SPIFFE in production environments.
Benefits include:
- Portable workload identities
- Strong service authentication
- Cloud-agnostic identity frameworks
These projects are increasingly used in zero trust architectures.
Machine Identity Lifecycle Management
Identity security isn’t just about authentication.
Lifecycle management matters just as much.
Provisioning
New workloads require secure identity issuance.
Automation is essential.
Rotation
Credentials must rotate regularly.
Short-lived credentials reduce exposure windows significantly.
Revocation
Compromised identities must be revoked immediately.
Delayed revocation creates major risk.
Expiration Monitoring
Teams need proactive monitoring to prevent outages.
Certificate expiration incidents remain surprisingly common.
Decommissioning
Unused machine identities should be removed promptly.
Dormant credentials create unnecessary attack surfaces.
Multi-Cloud and Hybrid Infrastructure Considerations
Modern enterprises rarely operate in a single environment.
Most organizations run combinations of:
- AWS
- Azure
- Google Cloud
- On-prem infrastructure
- SaaS platforms
- Edge systems
Each environment handles identities differently.
That fragmentation creates operational complexity.
Security teams often struggle with:
- Inconsistent IAM models
- Cross-cloud authentication
- Credential federation
- Unified policy enforcement
Federated identity approaches are becoming increasingly important.
Automation and Machine Identity Security at Scale
Manual management simply doesn’t scale anymore.
Modern environments require automation for:
- Certificate issuance
- Identity provisioning
- Secret rotation
- Policy enforcement
- Threat detection
Security orchestration platforms increasingly integrate machine identity workflows directly into DevSecOps pipelines.
Automation reduces:
- Human error
- Credential exposure
- Misconfiguration risk
- Operational overhead
But automation itself must be secured carefully.
Compromised automation pipelines can become catastrophic attack vectors.
Compliance and Regulatory Implications
Machine identity governance increasingly affects compliance programs.
Regulations now emphasize:
- Access control
- Encryption
- Authentication
- Auditability
- Least privilege
Industries facing heavy scrutiny include:
- Healthcare
- Finance
- Government
- Critical infrastructure
Frameworks commonly influencing machine identity programs include:
- NIST Zero Trust Architecture
- PCI DSS
- HIPAA
- SOC 2
- ISO 27001
Auditors increasingly ask organizations to demonstrate visibility into non-human identities.
Best Practices for Non Human Identity Security
Strong machine identity protection requires layered security practices.
Use Short-Lived Credentials
Short-lived tokens reduce attacker persistence opportunities.
Eliminate Hardcoded Secrets
Secrets should never live inside source code repositories.
Use centralized secret management systems instead.
Implement Mutual TLS
mTLS provides strong service-to-service authentication.
It’s particularly valuable in microservice environments.
Apply Least Privilege Access
Machine identities should only receive required permissions.
Avoid broad administrative access.
Rotate Credentials Automatically
Manual rotation creates operational risk.
Automation improves consistency and security.
Maintain Complete Identity Inventories
Organizations need visibility into:
- Active identities
- Associated permissions
- Expiration dates
- Ownership
Without inventory visibility, governance becomes impossible.
Monitor Behavioral Anomalies
Machine identities typically behave predictably.
Behavioral analytics can detect:
- Unusual access patterns
- Geographic anomalies
- Permission abuse
- Suspicious authentication attempts
Common Mistakes Enterprise Teams Make
Even mature organizations make avoidable machine identity mistakes.
Treating Machine Identities Like Human Accounts
The scale and behavior patterns are entirely different.
Machine identity governance requires specialized controls.
Ignoring East-West Traffic
Many organizations focus heavily on perimeter security while ignoring internal service communication.
Zero trust requires securing internal traffic too.
Overlooking Third-Party Integrations
External SaaS integrations often introduce unmanaged credentials.
These become blind spots.
Delaying Certificate Modernization
Legacy PKI infrastructure frequently struggles with cloud-native scale requirements.
Poor Ownership Tracking
Nobody knows who owns certain service accounts or certificates.
That creates operational and security problems.
Future Trends in Machine Identity Security
Machine identity security is evolving rapidly.
Several trends are reshaping the landscape.
Identity-Centric Security Models
Identity is becoming the new perimeter.
Network location matters less than verified trust.
Passwordless Infrastructure
Organizations increasingly replace static credentials with:
- Cryptographic attestation
- Hardware-backed trust
- Short-lived tokens
AI-Driven Identity Analytics
Security platforms are beginning to use AI for:
- Identity anomaly detection
- Credential abuse monitoring
- Risk scoring
- Automated remediation
Increasing Regulation
Governments and industry bodies are placing greater emphasis on identity governance.
Machine identity auditing requirements will likely expand significantly.
Workload Identity Standardization
Frameworks like SPIFFE may become foundational standards for cloud-native identity architectures.
FAQ Section
What are machine identities in cybersecurity?
Machine identities are digital credentials used by non-human entities like applications, containers, APIs, servers, and workloads to authenticate themselves securely within systems and networks.
Why are machine identities important in zero trust security?
Zero trust requires every entity to authenticate continuously. Since modern infrastructure depends heavily on machine-to-machine communication, machine identities enable secure authentication, authorization, and encrypted communication between services.
What is the difference between machine identities and workload identities?
Workload identities are a subset of machine identities specifically assigned to running workloads such as containers, Kubernetes pods, and cloud-native applications.
How do attackers exploit machine identities?
Attackers commonly target exposed API keys, stolen certificates, compromised service accounts, hardcoded secrets, and overprivileged machine credentials to gain unauthorized access.
What is machine identity protection?
Machine identity protection involves securing the lifecycle, usage, storage, issuance, rotation, and monitoring of machine credentials across infrastructure environments.
How does Kubernetes use machine identities?
Kubernetes uses service accounts, workload identities, and service mesh authentication mechanisms to secure communication between workloads and cluster services.
What role does PKI play in machine authentication?
PKI enables certificate issuance, trust validation, encryption, and cryptographic authentication for machine identities across distributed systems.
Why are short-lived credentials safer?
Short-lived credentials reduce the amount of time attackers can abuse compromised identities, limiting persistence opportunities.
What is SPIFFE?
SPIFFE is an open standard for securely identifying software workloads across dynamic and heterogeneous environments.
Are machine identities replacing passwords?
In many cloud-native systems, yes. Organizations increasingly rely on certificates, tokens, workload identities, and cryptographic authentication rather than traditional passwords.
Conclusion
Machine identities have quietly become one of the most important foundations of modern cybersecurity.
Cloud-native infrastructure, microservices, APIs, automation systems, and distributed workloads all depend on trusted machine-to-machine communication. As zero trust security models continue replacing perimeter-based architectures, machine authentication moves from a supporting role to a central security requirement.
The challenge isn’t just technical complexity. It’s scale.
Organizations now manage enormous ecosystems of certificates, workload identities, service accounts, secrets, and tokens across multi-cloud environments. Without strong governance, visibility, automation, and lifecycle management, those identities quickly become high-risk attack surfaces.
The companies building resilient zero trust architectures are the ones treating machine identity security as critical infrastructure — not a secondary IAM problem.
That shift is already redefining enterprise security operations.